Article on the subject of "instruction"
-

Fix Access Denied in Windows 7
in the following article, we will show you how to fix access denied when accessing shared folders on any computer using windows 7 operating system from another windows 7 computer located. in workgroup ...
-

Network analysis with Colasoft Capsa
two years ago, a computer worm appeared and raged around the world under the name conficker. they are primarily aimed at system vulnerabilities based on operating systems, user accounts ...
-

5 basic steps to protect your BitCoin account
when reading this article, many people will wonder what bitcoin is? it can be said that bitcoin is one of the best ideas ever in the virtual market, this is a system to use and convert virtual money units into real money, operating under a trade model. commercial, has a very high stability before
-

Monitor your child's activity through the Wireless Router
as the world becomes more and more modern with the continuous support of technology and computer science with the current speed, especially the internet environment, the management, supervision and education of children also become more complex than ever. while parents are trying to create a modern
-

New instructions in Intel's advanced encryption standard (AES-NI)
in this article we will show you the importance of encryption and go deep into intel aes-ni research.
-

Remove the folder's Lock icon in Windows 7
in the following article, we will present some basic steps to remove the folder lock icon in windows 7. whenever locking any folder, the system will appear a lock icon outside the folder. that, whether you can access it or not.
-

Compare Google Apps, Office 365 and Zoho Docs
when microsoft officially announced office 365 service, it was also the time when the company officially jumped into the online office application market. until now, microsoft has dominated in this field for the desktop platform, but with the online market it will be very difficult, because it will
-

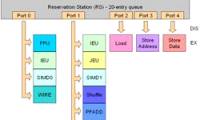
Inside Pentium M architecture
in this tutorial, we will show you how pentium m cpu works under the most understandable way. since all of intel's new cpus use pentium m architecture, this architectural research is a big deal
-

Connect your iPhone or iPod phone to Windows 7 via Bluetooth
in the previous tutorial, we presented some basic steps to connect mobile devices to windows computers via bluetooth. and this lane, we will continue with a product using the ios operating system, specifically between an iphone or ipod touch phone with a windows 7 computer.
-

Instructions for creating Business Card in Photoshop
in today's work, business card - business card is used very widely and popularly, whenever you need to talk with partners, customers or friends, this is exactly what you need. this business card contains many information about name, address, title, phone number, website, email ... of individuals or
-

Instructions for combining PowerPoint slides and videos
when watching the following clip, many people will realize that there is a perfect combination of slide shows and video presentations. so how to create such a combination?
-

Instructions for editing data in form of PDF file
fillable pdf form - forms available in pdf files for users to fill in data, usually they are very useful and convenient compared to printing that text file to paper and manually filling in information.
-

eQuiz - Multiple choice test on ASP
here is a small test of asp web programming language, a total of 30 questions will be answered with no time to answer each sentence.
-

Learn how Cache works (Part 3)
the cpu fetch unit will look for the next instruction to be executed in the l1 instruction cache. if it is not there, it will search on the l2 cache. after that, if not, it will have to access the ram to load the instruction.
-

What is ARM64? Important Features of ARM64
arm64 (advanced risc machine 64-bit) is a 64-bit microprocessor architecture based on the risc (reduced instruction set computing) instruction set.
-

9 experiences for new Android tablet users
getting used to a technology device is always a difficult challenge for most users. as for android tablets, too, in order to use fluently as well as understand all the functions of the product, it takes a lot of effort and research time.
-

Instruction for multi-nick Skype chat
guide multi-nick chat skype - skype is a very popular chat software because of its features. many people use skype to communicate at work or with friends and relatives, so using multiple skype accounts on one computer
-

Instruction for registration of Zing Vip MP3 to watch movies and listen to 320kbps quality music, Lossless
instruction for registration of zing vip mp3 to watch movies and listen to 320kbps quality music, lossless. you can download zing mp3 software in ch play with android or app store with ios, search keywords are 'mp3 zing' or 'zing mp3'.
-

The object () function in Python
the object () function in python returns an empty object. you cannot add new properties or methods to this object.
-

Instruction to watch movies with 2 subtitles (bilingual) in KMPlayer
instruction to watch movies with 2 subtitles (bilingual) in kmplayer
-

Instruction to delete Youtube search history (Delete Youtube History)
you can clear search history, delete watch history and privacy actions like videos. the following article will help you know how to delete history, set privacy on youtube.
-

COVARIANCE.P function - The function returns the covariance of a set, the product of the average of degrees of instruction for each pair of data points in Excel
covariance.p function: returns the covariance of the population, the average of the product deviations for each pair of data points in the two data sets syntax: covariance.p (array1, array2)
-

The origin of some familiar icons on the computer
the instruction symbol works on computers that are familiar to users every day, but few know about their origins.
-

Inside Pentium M architecture
in this tutorial, we will show you how pentium m cpu works under the most understandable way. since all of intel's new cpus use pentium m architecture, this architectural research is a big deal
-

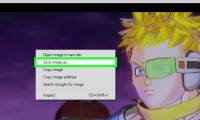
How to Save a Screenshot
screenshots have lots of uses, and most devices allow you to take them with quick shortcuts. screenshots can be used for troubleshooting, instruction, reference, or for showing off. the process for taking screenshots varies depending on...
-

New instructions in Intel's advanced encryption standard (AES-NI)
in this article we will show you the importance of encryption and go deep into intel aes-ni research.
-

How to Program in Brainf**K
brainfuck (commonly written as brainf**k to avoid swearing) is an esoteric programming language. it only has 8 instructions, so programs in brainf**k tend to be a bit long. however, each instruction is pretty easy to understand. get a...
-

Instruction to install an affordable price PC gaming rig, play during the holiday without worrying about lag with quality components not to be missed
installing a universal gaming computer is not easy but not easy. create your own super game battle with the quality products below can not be ignored.
-

Instructions for combining PowerPoint slides and videos
when watching the following clip, many people will realize that there is a perfect combination of slide shows and video presentations. so how to create such a combination?
-

Instructions for editing data in form of PDF file
fillable pdf form - forms available in pdf files for users to fill in data, usually they are very useful and convenient compared to printing that text file to paper and manually filling in information.
-

INSTRUCTION FOR ISA SERVER ENTERPRISE 2000 - IV
the most frequently asked questions about isa clients are: what is the isa client, what are the types, and which are used? all of these questions are necessary when you work with a complex system like isa server. the article provides an overview and how to deploy isa clients, exactly how
-

Instruction to register F @ st Mobile Techcombank fingerprint
after a while logging in, your f @ st mobile account will automatically log out, so you can replace the password with the fingerprint login on the f @ st mobile app for convenience.
-

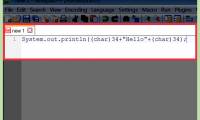
How to Print Double Quotes in Java
you've discovered that the double quote symbol ' will not work inside a java print instruction. you'll need to find an alternate way to tell the compiler to print this symbol, instead of interpreting it as instructions to close the string....