Article on the subject of "trojans"
-

Difference between Virus, Spyware and Malware
a flu virus develops and replicates by infecting cells on the body and turning them into virus replicating plants. in a place similar to a computer virus ...
-

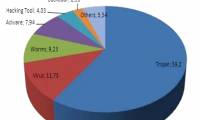
Around the world, about 50% of computers are infected with viruses
in january 2011, the world has about 50% of computers infected with viruses, this is the latest report of panda labs in vietnam, accordingly, these machines are mainly infected with trojans accounting for 59% .. .
-

Mobile code increased by 250% compared to 2009
the above information has just been announced by juniper global research center (usa). this has made many people startled, especially businesses.
-

Instructions to remove Safesoft Trojan (WIN32.Zafi.B virus)
symptoms of a computer infected with win32.zafi.b is that windows firewall will automatically appear accompanied by messages like 'security center alert' ...
-

Description of the P2P-Worm.Win32.BlackControl.g template
with the name p2p worm - they are mainly spread through peer-to-peer sharing models like kazaa, grokster, edonkey, fasttrack, gnutella ...
-

Description of template Trojan.Win32.Oficla.w
it can be said that this is a quite special type of malicious program - with different mechanisms and ways of operation compared to the previous known models.
-

Viruses are not only a threat to computers
experts say mobile devices and smartphones are becoming more and more 'prey' of the viruses, trojans, spyware ...
-

Information from Symantec about Hydraq trojan worms
the trojan.hydraq worm was used to exploit the zero-day vulnerability in internet explorer, reports from symantec.
-

'Fighting' virus to steal passwords
a newly emerged trojan from russia has 'outmaneuvered' a famous virus by stealing data and then removing malicious programs from the victim's computer.
-

Kaspersky launches antivirus version for Mac
kaspersky has just released a version of the antivirus software of the same name for apple's mac os x operating system.
-

Storm took advantage of the US national flag to spread
true to the predictions of computer security vendors that are extremely dangerous storm has returned to the right on july 4 - the us national day.
-

5 mobile security risks you need to avoid
here are the most used mobile attack methods of 2018. let's find out and see these new digital wave protections.
-

The most basic insights to becoming a Hacker - Part 1
many of you newbie have asked me 'what is a hack? how to hack? ' but you have forgotten that you need to have a general knowledge, understand the terms that people who are familiar with the web or use.
-

China - hacker 'factory'
with just a few keystrokes, the nickname hacker majia turned up the screen showing his latest victims.
-

Defeat China's largest hacker training furnace
chinese police have closed the website to recruit thousands of members and provide training on cyber attacks and malicious code.
-

Mistakes when using a password
while using online accounts such as mailboxes, banking services, passwords are like the anti-theft lock, the more sophisticated, the more secure the property.
-

What to do when the computer is poisoned
symptoms of computers when infected with a virus, how to prevent data to avoid being infected by malware!
-

10 most effective antivirus software for Windows 2019
the 10 best, free and most effective antivirus software on your computer, are highly appreciated for their popularity, updates and not taking up much of your computer's resources.
-

Attack analysis uses Excel 4.0 macros to disguise
on october 18, 2018, 360 threat intelligence center for the first time recorded an example of an attack using excel 4.0 macro to spread the trojan remote control imminent monitor.
-

Malware can steal Facebook, Twitter and Gmail accounts
researchers have discovered a new and complex malware variant, based on the famous zeus bank trojan but not just stealing bank accounts.
-

Can Trojans self-replicate?
trojans are one of the most insidious forms of malware that threaten our devices. they operate stealthily, often disguised as legitimate software or files, and cause huge damage.
-

Remove viruses, trojans on Windows 7 manually
this article i will show you how to remove viruses, trojans manually on windows 7 operating system in a simple way.
-

2 Dangerous Trojans are being distributed heavily through fake VPN webs
international cybersecurity researchers recently discovered a fake website that hides a vpn service, but is actually used to spread and install two malicious password-stealing trojans, vidar and cryptbot, into the network. victim's system.
-

The locations of viruses and trojans hiding during the boot process.
there are viruses and trojans that infiltrate your computer in a 'silently' way that you almost don't realize its change or harm. but then it will 'destroy' your system by entering some locations and is
-

Symbian S60 attack appears again
the malicious programmers have just recently 'created' a series of 3 new trojans that attack mobile devices using symbian s60 operating systems.
-

Trojans spread on Skype
according to the websense security monitoring company on march 22, skype is currently under attack by two malicious code names warezov and stration. warezov and stration are trojans that use infected computers to search and find
-

Introduction to viruses, worms, and Trojans
viruses, worms, and trojans are dangerous programs that can destroy your computer and information on your computer, slow down the internet, and use your computer to distribute them themselves.
-

VN: Online game password theft Trojan increased sharply
102 online password-stealing trojans appear in just one month, bringing the total number of online password-stealing trojans in vietnam to 258 from the beginning of 2007.
-

Distinguish viruses, trojans, worms and rootkits
most of us have heard of spyware, malware, viruses, trojans, worms or rootkits… but do you really know the difference between them? it's really not easy to understand all the terms that refer to these computer threats.
-

Detect hardware Trojans using machine learning technology
keysight technologies' experts claim that the combination of the cx3300's high-bandwidth high-resolution dynamic current measurement capabilities and keysight's ultra-fast clustering algorithm so far is an effective means of identifying trojans.
-

Viruses are not only a threat to computers
experts say mobile devices and smartphones are becoming more and more 'prey' of the viruses, trojans, spyware ...
-

Malware can steal Facebook, Twitter and Gmail accounts
researchers have discovered a new and complex malware variant, based on the famous zeus bank trojan but not just stealing bank accounts.
-

Use SEO to bring Google search results to bank trojans
when you think you know all the tricks, malware teachers always have new tricks that surprise you.
-

How to remove Trojan, Virus, Worm or Malware?
these are extremely dangerous programs. when your computer is attacked by a virus or malware, they will start to devastate your computer.
-

Around the world, about 50% of computers are infected with viruses
in january 2011, the world has about 50% of computers infected with viruses, this is the latest report of panda labs in vietnam, accordingly, these machines are mainly infected with trojans accounting for 59% .. .
-

Differentiate types of malware
some people have a habit of calling all malicious software (malicious software) under a common name as computer virus, but this is completely incorrect. viruses, worms and trojans are different types of malicious software with different behaviors. in particular, they spread themselves in many
-

Facebook Ads Manager becomes a victim of Trojan information theft
an unknown hacker group is distributing a trojan stealing information disguised as a pdf reader that can copy facebook session cookies
-

BankBot is back on Play Store - an uninterrupted story about malware on Android
after google's efforts to block malware from play store, malicious applications still find ways to trick android anti-malware and poisoning tools.
-

Detected 4 banking trojans in 11 apps on Google Play Store
banking trojans are designed to steal banking credentials and other sensitive data.
-

10 free security downloads
spyware, viruses, trojans and other malicious software are everywhere on the internet, all of them want to jump into your computer and perform destructive behaviors.