Article on the subject of "encryption"
-

Wi-Fi Enterprise and 802.1X encryption in Mac OS X
in this tutorial, i will show you how to configure and connect wpa / wpa2-enterprise networks in leopard and 10.6 snow leopard.
-

New instructions in Intel's advanced encryption standard (AES-NI)
in this article we will show you the importance of encryption and go deep into intel aes-ni research.
-

Switch to WPA / WPA2-Enterprise encryption
in this article, we will show you two very different modes of accessing a protected wi-fi network.
-

Learn about Pumas extortion software
this article will provide you with basic information about pumas malware, as well as ways to help you completely remove this malware.
-

Tool to unlock data encryption sessions - CAPTCHAS
recently, two researchers have released a tool that can be used to unlock encrypted data via the web server system contained in cookies and hidden characters in html pages.
-

10 important information you should know about Windows computers
have you ever felt embarrassed when someone asked about the version of windows you are using? do you know the amount of ram installed on your device? information like this is very important to users when troubleshooting. therefore, this article will look at some of the information users need to
-

Anti-theft solution for laptops
previously, losing a laptop (laptop) always meant losing important data of users on it. however, users now have many methods to save this image, can regain control of important data on it.
-

Lenovo IdeaPad V460 is for office workers
lenovo's new laptop products are equipped with core i chips, along with the ability to change graphics cards and luxurious designs ...
-

Set up ProFTPd with TLS on Ubuntu 11.04
ftp is a popular file transfer protocol used today. however, this protocol gradually becomes less secure because the entire password and data of the file is transmitted as clear text.
-

Instructions to encrypt and 'hide' BitTorrent traffic data
through the previous analysis articles on tipsmake.com, we understand the basics of bittorrent as a form of storing and sharing files and data online. besides, the transmission and sharing of unallocated files and data is a contradictory form, for example when we use and download files from a fixed
-

Encrypt email in Outlook 2007
the following article will guide you step by step to encrypt email in outlook 2007.
-

Set password to protect and encrypt documents in Office 2013
the password and document encryption feature in office 2013 is applicable for both word, excel and powerpoint and is very effective in protecting sensitive data despite extremely simple implementation. however, many people may be unfamiliar with these two great features. the article will show you
-

Can data encryption protect you from Ransomware?
many people believe that data encryption is a useful way to prevent ransomware from stealing user information. is that true? read the article below to know more!
-

Some common data security measures
data protection is extremely essential, because data is the most important asset of users on computers. it can be said that the need to use computers and networks comes from data.
-

Microsoft changes the default settings to keep the content stored on the hard drive safe
in june last year, security researchers discovered that the method of securing ssd hard drive encryption could be easily 'broken' ...
-

Mozilla released Firefox Send - a free encrypted file sharing service
mozilla has finally officially released a complete version of firefox send, a free encrypted file transfer service, allowing users to share files from any browser.
-

Application protection against DFA attacks
differential fault analysis, also known as dfa, is an attack technique designed to recover cryptographic keys from the application ...
-

Cr1ptT0r Ransomware spreads on D-Link NAS devices, targeting embedded systems
a new ransomware software called cr1ptt0r is built for embedded systems that target network attached storage devices (nas) that have been spread over the internet, and have the task of encrypting data available on infected devices. .
-

Microsoft shook hands with VirusTotal in resolving malicious code issues that affected MSI files
microsoft and the chronicle's virustotal team have teamed up to develop tools to make warnings faster and more accurate for modified msi files to turn into malicious java code repositories.
-

What is end-to-end encryption? How does it work?
online privacy is the need of the times. especially when there is a continuous increase in the number of techniques to steal user data.
-

5 popular encryption algorithms you should know
you have heard or used encryption and know how important it is. most internet services use encryption to keep user information safe. however, coding is still something difficult to understand. there are many types of encryption and are used for many purposes. how do you know the 'best' encoding?
-

Coding is not as difficult as you think
once you learn and actually try it out for yourself, you will find that encryption is incredibly easy to use and incredibly practical for everyday life.
-

Top 5 best USB encryption software
all data needs to be secure - especially with a small usb, which can easily be lost or stolen.
-

What is Zero-Knowledge Encryption? Why use this type of encryption?
data breaches are becoming more and more common, so it's essential that you know about the different ways you can protect your valuable information. zero-knowledge encryption is one of the methods that provides superior privacy and data protection.
-

Discover the difference between symmetric and asymmetric encryption
there are two commonly implemented types of encryption: symmetric and asymmetric. the fundamental difference between the two types of encryption is that symmetric encryption uses a unique key for both encryption and decryption.
-

Top 20 best encryption software for Windows
in a pc, many of your personal information may be accessed illegally. that's because windows data is stored on the drive that is not encrypted or protected by encryption software so anyone can access your private and confidential information.
-

Adiantum, Google's new encryption method helps ensure safety for all Android devices
with the goal of bringing memory encryption to low-cost android devices while ensuring their performance, google recently officially lost a new encryption method called adiantum.
-

What is data encryption? Things to know about data encryption
data encryption is to transfer data to a new form that users cannot read and need to use the key to encrypt the data.
-

File encryption software and privacy protection messages
recently, reports have shown that technology spying is on the rise. therefore, it is necessary to protect your data and privacy with encryption software. the following article will introduce you to some great encryption software for windows, ios and android.
-

How to enable Full-Disk Encryption on Windows 10?
on windows 10, some use encryption by default, but some do not. in the following article, network administrator will show you how to check if the memory on windows 10 computer is encrypted.
-

How to set up military-grade encryption on Windows 11
military-grade encryption is a term marketers use to describe aes. aes itself stands for 'advanced encryption standard', a very secure way to encrypt digital data.
-

Why ISPs Hope You Don't Know Why DNS Encryption Protocols Are Different
the good news is that you can encrypt those dns requests to prevent prying eyes from seeing the websites and services you're using.
-

How to encrypt text using the Text Encryption Tool
text encryption tool is a text encryption utility with sha-256 algorithm, which helps you quickly encrypt or decode text.
-

Instructions for USB encryption with VeraCrypt
usb (removable drive) is a place to store your important files. what will happen if you lose it? the result will be extremely bad so it is better to encrypt your usb. in this article, tipsmake.com will guide you how to simple and effective usb encryption.
-

How to encrypt email
if not encrypted, your email is at risk of being hacked and read at any time, or you may lose your account. this article will give you an overview of how to encrypt email, help you understand and choose the right encryption solution.
-

Microsoft changes the default settings to keep the content stored on the hard drive safe
in june last year, security researchers discovered that the method of securing ssd hard drive encryption could be easily 'broken' ...
-

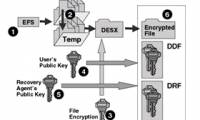
How to back up the EFS file encryption key and certificate in Windows 10
encrypting file system (efs) is an encryption tool built into windows that is used to encrypt files and folders on ntfs drives, to protect them from unwanted access.
-

Automatically encrypt EFS in Windows XP, Vista or Windows 7
in the following article, we will show you how to create scripts to automate the efs standard data encryption process of user accounts every time they log in. the purpose of encryption in this way is to protect confidential documents, information of individuals, organizations or companies, then
-

What is the difference between password locking and encryption?
in cybersecurity, nothing is more important than keeping sensitive information private and safe. everyone should make an effort to do so, from individuals to large organizations.