Article on the subject of "cyberattacks"
-

How to set up a website with Project Shield: DDOS prevention service from Google
despite having the same name as nvidia's handheld game console, google's project shield is a completely standalone project that will be of great help to small websites.
-

Things You Can Do to Protect Yourself from Cyberattacks
technology is progressing at such a rapid rate that it's become very hard to keep up with the latest update and features that new state-of-the-art systems apply.
-

Microsoft urgently warns about a phishing campaign that uses malicious Excel macros to hack PCs
security team with microsoft's security intelligence has issued an urgent warning about a massive fraud campaign.
-

Supercomputers across Europe were hacked to exploit virtual money
the attack forced these supercomputers, including a supercomputer participating in research on covid-19, to be shut down to conduct investigations and remediate consequences.
-

A series of supercomputers in Europe were suddenly attacked
the number of supercomputers affected in this incident amounted to more than 12.
-

Customer data collected during Capital 14's 14 years was stolen
this may be considered the biggest data theft ever recorded in the us.
-

Facebook is a new trend in cyber attacks
attack through mxh, specifically facebook is becoming a new trend, very dangerous in the current cyber attack, mr. vu quoc thanh, vice president and secretary general of vnisa said at the information security day 2014 held yesterday (november 4).
-

Chinese hackers use Dropbox, WordPress attacks Southeast Asia
the chinese cybercrime gang dnscalc has added dropbox and wordpress to the list of malware distribution tools. their goals are government-related individuals and organizations.
-

Hacker earned $ 32,000 in 7 weeks by fixing a series of gaps in e-money projects
over the past 7 weeks, white-hat hackers around the world have earned at least $ 32,150 through the successful fix of a series of security flaws that appear on popular electronic and blockchain platforms like tron, brave, eos and coinbase.
-

The hacker group threatened to spread the network attack tool behind WannaCry
the tool used by the hacker group to create the wannacry global cyber attack is about to be released.
-

Things You Can Do to Protect Yourself from Cyberattacks
technology is progressing at such a rapid rate that it's become very hard to keep up with the latest update and features that new state-of-the-art systems apply.
-

Google warns hackers are abusing Gemini to accelerate cyberattacks.
google says that state-backed hacking groups are using gemini to accelerate cyberattacks, from target research to vulnerability exploitation.
-

How to set up a website with Project Shield: DDOS prevention service from Google
despite having the same name as nvidia's handheld game console, google's project shield is a completely standalone project that will be of great help to small websites.
-

Microsoft warns hospitals about VPN cyberattacks during coronavirus
the tech giant notes that as more people work remotely, a new breed of hacker could attack.
-

The UN acknowledges that cyberattacks are extremely sophisticated and cannot identify the culprit
the united nations recently acknowledged the organization was the target of a massive cyberattack in the summer of 2019.
-

Supercomputers across Europe were hacked to exploit virtual money
the attack forced these supercomputers, including a supercomputer participating in research on covid-19, to be shut down to conduct investigations and remediate consequences.
-

A series of supercomputers in Europe were suddenly attacked
the number of supercomputers affected in this incident amounted to more than 12.
-

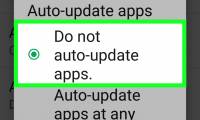
How to Turn Off Google Chrome Updates Completely
today's tipsmake will show you how to prevent google chrome from automatically updating on windows, mac, iphone and android platforms. note that stopping updating google chrome puts your device and other devices and systems at risk of hacking or cyberattacks.
-

Customer data collected during Capital 14's 14 years was stolen
this may be considered the biggest data theft ever recorded in the us.
-

The hacker group threatened to spread the network attack tool behind WannaCry
the tool used by the hacker group to create the wannacry global cyber attack is about to be released.
-

The new algorithm can prevent cyber-attacks on GPS devices
scientists have developed a new algorithm that can help detect and prevent cyberattacks on gps-enabled devices in real time.
-

What is BlueSmack attack?
as people become increasingly connected through technology, the vulnerability of devices to cyberattacks continues to increase. one such threat is the bluesmack attack targeting bluetooth-enabled devices.
-

5 things not to be shared with AI chatbots
there are inherent risks associated with using ai chatbots, such as privacy concerns and potential cyberattacks. it is important to exercise caution when interacting with chatbots.
-

Even mobile sensors can become phishing attacks
the complexity and sophistication of cyberattacks are always in line with the development of the internet world.
-

6 webcam security tips everyone should know
threats, from cyberattacks to unauthorized surveillance, are real, but you can prevent intruders from accessing your webcam and invading your personal space.
-

5 secure password alternatives you should consider
with the rise of cyberattacks targeting password-based authentication and serious data breaches, passwords don't seem like a safe solution anymore.
-

What is botnet DDoS?
as the number of iot devices continues to grow, fears of cyberattacks also increase. one of the main sources of attack is ddos botnets targeting unsecured iot devices.
-

Phishing attack: The most common techniques used to attack your PC
phishing attack is probably a term that is not unfamiliar to most internet users. in fact, it is also one of the most common forms of cyberattacks.
-

Chinese hackers use Dropbox, WordPress attacks Southeast Asia
the chinese cybercrime gang dnscalc has added dropbox and wordpress to the list of malware distribution tools. their goals are government-related individuals and organizations.
-

IBM embarked on FPT to distribute new network security solutions
in the context of many experts warning about the explosion of cyberattacks and the increasing complexity of current cyber threats, ibm has partnered with fpt trading company (fpt trading) to introduce new network security solution ibm security network protection xgs 4100