Article on the subject of "devices"
-

5 HBO Max tricks to get the most out of your new streaming subscription
everything you need to know about parental controls, managing devices, downloads and more.
-

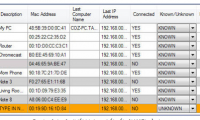
How to check who is using your home WiFi 'temple'
to find out if anyone is using the wifi temple of your home, your hostel, ... or not is not too difficult work after reading this article.
-

My WIFI Router - Free and convenient Wifi Broadcasting Software
my wifi router is a software that turns laptop or desktop computers with wifi card into an easy wifi hotspot. free, effective, fast and no junk software.
-

How to Remotely Wipe SugarSync Files on a Device
with sugarsync, you won't need to worry about your files' security and privacy on your devices when they get lost or stolen. even if your devices fall in the wrong hands, you can ensure that your files don't. sugarsync has a remote wipe...
-

How to Connect HDMI Cables
this wikihow teaches you how to use hdmi cables to connect computers, entertainment systems, and game consoles to tvs. hdmi allows you to quickly connect your electronic devices without having to fumble with color-coded cables or multiple...
-

Learn about 802.11ac standard Wifi
theoretically, 802.11ac is capable of transmitting a maximum of 1.3gbits / sec (162.5 mb / sec), the traffic of an 802.11ac router twice the traffic of 802.11n routers.
-

UWB Technology: Promising future
the uwb (ultra-wideband wireless) wireless technology promises to replace not only irda and bluetooth technology, but also a wireless revolution in the home. like other mainstream technologies, uwb targets home users. people
-

Basically about Wireless Networking
wireless networking (wireless networking) is a new solution for office, home, or large network models where ethernet networks cannot work. installing a basic wireless network is simpler than the ethernet (wired network) network, and you can easily import more pcs or other devices to the network.
-

Power over Ethernet cable
tcp / ip protocol on the ethernet platform is very popular in today's communication market. the success of ethernet-based technologies is in part due to the very active cooperation in the development of common standards. this success will also create new strengths on existing infrastructures such
-

Simplify security
keeping your pc safe is a problem. you need to run anti-virus software, anti-spyware, firewall, fake detection tool bar ... and everything above must be updated and tightly managed. this new type of security device promises to simplify this issue and n
-

How to secure Bluetooth devices
with the ability to connect to other devices such as a wireless network within a distance of 9m, bluetooth is an integrated technology in a variety of devices from mobile phones, personal pda assist devices and computers. portable to vehicles & o
-

Symbian S60 attack appears again
the malicious programmers have just recently 'created' a series of 3 new trojans that attack mobile devices using symbian s60 operating systems.
-

2006 - year of mobile malware
according to a study published yesterday by mcafee avert labs, in 2006, the threat of mobile security will triple when smartphones and other mobile devices are available. become popular.
-

Reuse old computers
today's old computers are not no longer usable, but still have performance but consumers because of the 'life' of new machines should not be used.
-

The first 10 WiMax products meet the standard
the wimax forum claims the first 10 mobile wimax products to meet the standard for 2.5ghz frequency. certification for the 3.5ghz frequency product will be carried out at the end of 2008.
-

8 useful tools for mobile employees
today's mobile workers are more and more devices and along with it are more and more problems. this is the way to help you simplify unnecessary items when traveling.
-

Six tips for adding wireless devices to your work environment
wireless mobile devices such as blackberries, smart phones, pdas have wifi and windows tablets supported more and more everywhere. these devices are the most popular devices of wireless networks, more than desktops and m
-

Internet's 'Father' and the interplanetary protocol
32 years ago, two computer scientists vinton g. ceft and robert e.kahn sat together at a hotel in palo alto, california, usa, and outlined code to strengthen the network. internet.
-

Blade Server - New server architecture
suppliers are advertising blade servers as a new architecture to replace traditional server designs - stand alone or rack-mounted. however, experts also c & og
-

Beyond iOS 10, iOS 11 is installed on 47% of devices
only about 3 weeks after the public release, ios 11 usage rate has reached 47%, completely surpassing ios 10.
-

10 Smartphone Devices That Have Replaced Them Forever
smartphones have replaced so many other devices. they are so versatile that you probably don't need any of the categories of devices they replace.
-

How to secure Bluetooth devices
with the ability to connect to other devices such as a wireless network within a distance of 9m, bluetooth is an integrated technology in a variety of devices from mobile phones, personal pda assist devices and computers. portable to vehicles & o
-

Six tips for adding wireless devices to your work environment
wireless mobile devices such as blackberries, smart phones, pdas have wifi and windows tablets supported more and more everywhere. these devices are the most popular devices of wireless networks, more than desktops and m
-

The 6 Most Vulnerable Devices in Your Home
our homes are filled with devices that simplify our lives and keep us connected, but many of them are surprisingly easy targets for cybercriminals.
-

11 ways to keep IoT devices safe
hackers are increasingly targeting iot devices to steal data, install malware, or use them in botnets. so, following iot device security best practices has become more important than ever.
-

Good tips for Android devices
sometimes cleaning android devices means you will have to delete a lot of files to free up storage space. if you want to remove the rubbish from the android device's internal memory for a more streamlined arrangement, our article will help you do it in the most consistent way.
-

This critical vulnerability turns home devices into attack tools
vulnerabilities in millions of iot devices could allow attackers to view live camera feeds, create botnets, or use the attacked device as a springboard for further attacks.
-

Errors on mobile applications allow hackers to control LG devices
lg electronics tried to avoid a security disaster when working with researchers to patch vulnerabilities in mobile applications that customers use to control lg smart home devices.
-

8 to-do list apps sync on all devices
a to-do list is only useful if you can access it as soon as you need it. if you own multiple devices, you may have trouble accessing your list from each of those devices.
-

What is RFID? What role does RFID play in IoT devices?
radio-frequency identification (rfid) is a popular technology in production to identify, record and control moving objects.
-

6 Apple devices not recommended to buy at the moment
there are some apple products that you should not buy right now because apple may stop supporting them in the near future.
-

Google launched TensorFlow Lite 1.0 for mobile devices and embedded devices
google today has officially introduced tensorflow lite 1.0, a developer-only tool for deploying ai models on mobile devices and iot.
-

How to classify Bluetooth devices and accessories on iOS
ios 14.4 has just been updated by apple features that allow users to categorize bluetooth devices and accessories. the purpose of this classification is to help devices operate more stably on the iphone and ipad.
-

Review Logitech K480: Keyboard with the ability to connect multiple mobile devices
the logitech k480 is an overall good quality keyboard for mobile devices. the keyboard has a nice table holder for tablets or phones.
-

Mobile messaging in Exchange 2003 (Part 2): Discover security policies
we all know that mobile devices are very likely to be lost or stolen. when synchronizing devices with mailboxes, there is a need to protect our devices, the purpose is also to
-

List of devices upgraded to iOS 12
according to apple, ios 12 will support all devices running chips with 64-bit platforms, ie devices that support ios 11 will be upgraded to ios 12. and this is the list. details of devices are upgraded to ios 12 officially on the apples homepage.
-

Android devices will be 'stamped' trademarks
although dominating on mobile devices, google will soon increase its presence on android devices with a certification logo.
-

What kind of device will shine with Windows 8?
with the exit of the traditional mouse-and-keyboard model, windows 8 opens the door to many new devices, retooling for old devices. but which one will work best?
-

Why you should rename an audio device in Windows 10 and how
have you ever felt confused when managing audio devices such as speakers, headphones, microphones… on windows 10? to make it easier to identify connected audio devices on your system, give each device a specific name.
-

How to fix 'Connected Devices Platform User' service error using up RAM on Windows
when it consumes too much ram, it means there could be a problem with the process or your connected devices. the article below will show you how to prevent the connected devices platform user service from taking up your physical memory.