Article on the subject of "phishing"
-

List of 114 fake virus removal programs
the malware tricked users into installing and paying for fake anti-virus software without cleaning the computer, nor protecting it against viruses.
-

How to protect yourself from phishing attacks via mobile phones
mobile phones are a great gadget, and it has marked a huge change in the lives of each of us. combined with the internet, smart phones help users have access to a huge amount of data whenever you need it.
-

What is Office 365 Attack Simulator? How to use it?
you can train your employees to identify such attacks using office 365 attack simulator. this article will introduce some methods to simulate phishing attacks.
-

How Phishing works
in the previous post, we learned how to avoid facebook scam. today, we will learn more about how phishing works.
-

Small businesses how to fight hackers?
hackers can crash websites, destroy data and may have other bad behaviors for your corporate network ...
-

What is Spear Phishing?
you may have encountered spear phishing. when using this technique, cyber criminals will send you a message from an audience you know, asking you to provide your personal information.
-

How does eFencing work?
one of the biggest concerns for the bidder is to pay a large sum of money for an item that only receives bad products or even doesn't receive anything.
-

How to block phishing attacks in Firefox 3
phishing evolved from the previous phreaking, a form of attack on long-distance telephone systems for free calls. however in phishing, the level of influence is many times greater.
-

Microsoft shows how to avoid trapping phishing
microsoft has issued a warning and recommended ways to protect users of e-mail services ...
-

How do hackers attack your Facebok account and how to prevent this process?
hackers can attack your facebook account in many different ways, such as attacking email addresses, phishing .... to better understand how hackers attack your facebook account and solutions to prevent this process, please refer to the following article of network administrator.
-

How to hack Gmail's two-step authentication
two-factor authentication does not mean that you are absolutely safe against phishing attackers.
-

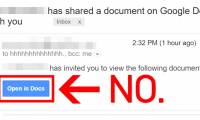
A lot of Gmail accounts are attacked by fake Google Docs
if you receive a google docs file sharing email today, it's best not to click, even if it's from an acquaintance.
-
![[Infographic] How to recognize and prevent Phishing attacks](https://tipsmake.com/img/no-image.png)
[Infographic] How to recognize and prevent Phishing attacks
there are dozens or even hundreds of emails sent to your inbox every day. so how do i know they are not phishing attack emails?
-

India's largest IT services company is hit by a hacker '
the giant in the field of providing it services in the world's second most populous country, wipro ltd, based in bengaluru, karnataka, india, has become the latest name and also the most lucrative. join the list of businesses that are victims of phishing attacks in 2019.
-
![[Infographic] 4 types of Phishing are easy to trap users](https://tipsmake.com/img/no-image.png)
[Infographic] 4 types of Phishing are easy to trap users
phishing often appears as a reliable activity by legitimate companies or a reputable electronic information site like ebay, paypal, gmail ..
-

25% of 'over-the-counter' phishing emails are the default security of Office 365
a recent report showed that as many as 25% of all phishing emails were found after researchers conducted a series of 55 million emails that had previously been office 365 exchange online. protection (eop) - office 365's default security program is marked as' clean 'and of course has been reached by
-

Detecting new electronic phishing malware, redirecting payment transactions to attackers
recently, cyber security experts have discovered the latest type of attack from the electronic money world, silently redirecting payment transactions made to attackers instead of intended recipients.
-
![[Infographic] 4 types of Phishing are easy to trap users](https://tipsmake.com/img/no-image.png)
[Infographic] 4 types of Phishing are easy to trap users
phishing often appears as a reliable activity by legitimate companies or a reputable electronic information site like ebay, paypal, gmail ..
-

What is Spear Phishing?
you may have encountered spear phishing. when using this technique, cyber criminals will send you a message from an audience you know, asking you to provide your personal information.
-

5 signs to identify phishing websites
when it comes to online security, there's one age-old problem: phishing. many people receive phishing content through email or social media platforms.
-
![[Infographic] How to recognize and prevent Phishing attacks](https://tipsmake.com/img/no-image.png)
[Infographic] How to recognize and prevent Phishing attacks
there are dozens or even hundreds of emails sent to your inbox every day. so how do i know they are not phishing attack emails?
-

Why hackers switch to phishing attacks beyond email and how to prevent them
phishing attacks today extend beyond email to social media, text messages, and advertising. find out why this trend is so popular and how your business can protect itself.
-

How to identify phishing emails
according to statistics from email security firm mailfrontier, only ... 4% of users are able to identify phishing emails at 100% accuracy rate.
-

How to protect yourself from phishing attacks via mobile phones
mobile phones are a great gadget, and it has marked a huge change in the lives of each of us. combined with the internet, smart phones help users have access to a huge amount of data whenever you need it.
-

How to report phishing emails in Outlook.com
phishing email is a seemingly legitimate email, but it was created to steal personal information, such as account numbers, usernames, pins or passwords.
-

Phishing attack: The most common techniques used to attack your PC
phishing attack is probably a term that is not unfamiliar to most internet users. in fact, it is also one of the most common forms of cyberattacks.
-

Phishing emails are getting more sophisticated, can you spot them?
if you thought phishing emails were just poorly written messages asking you to help a distant prince move millions of dollars out of his country, you need to be wary of today's much more sophisticated scams.
-

Learn about the Adversary-in-the-Middle phishing attack method
phishing attacks are extremely common right now. this method of cybercriminals can be very effective in stealing data and does not require a large amount of work at the grassroots level.
-

4 tools to detect phishing emails
email phishing is no longer as simple as it used to be. scammers are now tech-savvy criminals who leverage advanced tools to scam victims.
-

25% of 'over-the-counter' phishing emails are the default security of Office 365
a recent report showed that as many as 25% of all phishing emails were found after researchers conducted a series of 55 million emails that had previously been office 365 exchange online. protection (eop) - office 365's default security program is marked as' clean 'and of course has been reached by
-

What is Callback Phishing? How to fight it?
if you've ever received an email asking you to renew your service or pay a bill for a service you never purchased, you've encountered callback phishing.
-

Microsoft shows how to avoid trapping phishing
microsoft has issued a warning and recommended ways to protect users of e-mail services ...
-

What is IPFS Phishing attack? How to avoid?
while the interplanetary file system (ipfs) offers many benefits, it also allows cybercriminals to carry out malicious campaigns.
-

Identify popular online scams so as not to lose money unfairly
phishing via facebook, zalo, phone calls ... is quite common, although it has been warned but there are still many people who are 'trapped'. find out the tricks, phishing tricks of scammers through the following article to not lose money unfairly and avoid unwanted nuisance.
-

How is Phishing used to steal NFTs?
as is the case with most industries, when a product begins to gain significant value, it becomes a target for criminals to profit.
-

Warning: Phishing attacks targeting Microsoft Teams show signs of sharp increase
microsoft teams is reluctant to be the new target that online scammers are targeting.
-

GitHub is under strong phishing attack, users pay attention to account security
github - the world's largest open source software repository, is now the target of a phishing attack campaign.












![[Infographic] How to recognize and prevent Phishing attacks](https://tipsmake.com/img/no-image.png)

![[Infographic] 4 types of Phishing are easy to trap users](https://tipsmake.com/img/no-image.png)


![[Infographic] 4 types of Phishing are easy to trap users](https://tipsmake.com/img/no-image.png)


![[Infographic] How to recognize and prevent Phishing attacks](https://tipsmake.com/img/no-image.png)


























![[Infographic] How to recognize and prevent Phishing attacks](https://tipsmake.com/data/thumbs_200x120/[infographic]-how-to-recognize-and-prevent-phishing-attacks_thumbs_200x120_uJR0hPgYg.jpg)

![[Infographic] 4 types of Phishing are easy to trap users](https://tipsmake.com/data/thumbs_200x120/[infographic]-4-types-of-phishing-are-easy-to-trap-users_thumbs_200x120_TYXfXnKZL.jpg)














