Article on the subject of "permissions"
-

How to Change File Permissions on Windows 7
permissions in windows 7 determine which users can access, modify, and delete files and folders. every file and folder on your windows computer has individual permissions settings. changing permissions allows you to lock down or open up...
-

Learn about Permission and Role Based Access Control - RBAC part 2
in the previous section of the article, we showed you how to set up and configure the level of authorization with rbac - role based access by deploying predefined role groups via the graphical interface of the exchange control panel. however, when faced with the need to set more decentralization
-

Efficiently exploit printers in Windows Server 2003 (Part 2)
in part 1 of this article, i have shown you how to configure single printers to manage managed printers on a server running windows server 2.
-

Techniques for decentralizing Window administration
today group policy is becoming more important and has more options for delegation. understanding where to set permissions and how to delegate certain tasks can help you establish a safe and efficient network.
-

Control of resource terms
everyone knows that it's important to lock up and protect your resources online. the resources that need to be protected here include folders, files contained in them, as well as some registry keys that are placed on your computer.
-

Learn about Firefox's about page system
essentially, mozilla's firefox browser contains a lot of options to 'set up' settings, specifications ... to be 'hidden' in their about page. we can access those pages by typing the address about: and the corresponding name in the address bar. here, you will find a lot of different information,
-

Why should you always check app permissions before pressing install?
taking a moment to review your app permissions can save you a lot of privacy and security problems later on!
-

How to Change File Permissions on Windows 7
permissions in windows 7 determine which users can access, modify, and delete files and folders. every file and folder on your windows computer has individual permissions settings. changing permissions allows you to lock down or open up...
-

How to use the temporary permission feature of Android 11 on any phone?
not everyone uses pixel phones. that means you are not likely to experience the latest android 11 features. the following article will tell you how to get temporary, one-time permissions on android 11 without rooting.
-

How to edit application permissions on Android
some applications such as pitu, when installed on android devices, require users to accept the terms, which is to access some settings on the device such as location, contacts, phone numbers, ... this inadvertently provided personal information for the application.
-

5 best tools to manage app permissions on Android
have you ever installed an app and found it suspicious asking for too many unnecessary permissions on the first run?
-

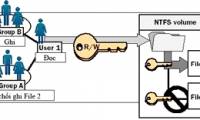
Network basics: Part 20 - File level permissions
in the previous part of this series, we introduced shared folders that can be protected using share level permissions or ntfs permissions.
-

How to decentralize users in MS SQL Server
administrators can create, delete or deny permissions in ms sql server. the permissions here refer to database access (csdl). you can create, delete or deny permissions in ms sql server.
-

Distribute file access with chmod command
unix and linux operating systems decentralize access to files and directories using three access parameters, read (read), write (write) and execute (run) to delegate permissions to three groups of objects, including: system owners, administrative groups and users.
-

How to assign Administrator permissions on a Windows 7 computer?
if you use windows 7, in some situations you will encounter an error that the system does not assign admin rights to store, use some programs on the hard drive system .... to fix this error you can refer to some answers below.
-

How to assign permissions to delete any folder or file on Windows?
in some cases when you delete a folder or file on a windows computer but cannot delete it and on the screen that displays an error message you need permission to perform this action. in order to be able to delete folders and files, you must assign permission permissions to delete them.
-

Techniques for decentralizing Window administration
today group policy is becoming more important and has more options for delegation. understanding where to set permissions and how to delegate certain tasks can help you establish a safe and efficient network.
-

6 Linux permission commands every admin needs to know
you need to master some linux terminal permission commands and below are the top terminal commands that you should memorize.
-

Configure IIS for an FTP Site - Part 4
in this article, i will conclude the series of tutorials on how to configure ftp sites by introducing permissions and permissions to work in iis 7.
-

How to set edit permissions for spreadsheets in Google Sheets
knowing how to set editing permissions for spreadsheets in google sheets helps you use google sheets effectively, allowing you to easily grant or restrict access to everyone who can view and edit your spreadsheets.
-

How to enable / disable site permissions in Microsoft Edge
if you want / do not want websites to access certain things, you can block or allow arbitrary. here's how to manage websites that have access in microsoft edge.
-

How to check application access on macOS
many applications installed on macos need to access some content such as cameras, contacts, microphones, etc. so how to review the permissions of applications on macos?
-

File permissions / access mode in Unix
file ownership is an important component of unix that provides a secure way to store files. every file in unix has the following properties to represent access rights to it.
-

Why does USB drive, memory card ... use FAT32 format instead of NFTS?
fat32 does not support file permissions. with ntfs, you can assign permissions to access, edit or delete files to increase system security.
-

User Permissions on Server - Who Should Have What Permissions?
server user authorization: who should have what rights? is an important issue in modern information system management.
-

How to Delete Read-Only Files on Linux
there are several ways to help you delete files read-only on linux. if it's a file you own, you can change the file permissions or use the sudo command to delete the original file. however, if you cannot delete files with write permissions (or see a 'read only file system' error message), you need