Article on the subject of "rule"
-

Application security with AppLocker
applocker is a new integrated tool on windows 7 and windows server 2008 r2 helps block unwanted applications on the network.
-

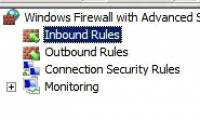
Overview of Windows Server 2008 Firewall with advanced security features - Part 2
in the first part of this three-part series, we introduced some global configuration settings for using a firewall. in this section, we will introduce the inbound / outbound rules so you can control incoming and outgoing connections
-

Use Snort to detect some of the current popular attacks on Web applications
according to statistics from leading security company acunetix, recently the number of attacks on web applications has increased rapidly (75% of the attacks are done in the application layer. web) [see 1]. in which two attack techniques commonly used by hackers are cross-site scripting and sql
-

Create a Rule to move and store email to another folder in Outlook
if multiple emails are received from the same sender every day, why not create a separate folder for that address.
-

What can be learned through 4 spiritual rules of Indians?
nothing in this world happens randomly.
-

Learning the 1-3-1 Rule Can Save You From Travel Nightmares
flight canceled or delayed? you'll be able to rebook and get to your destination with this smart travel tip using the 1-3-1 rule.
-

Explain the rule 30-30-30 when resetting the router
technology enthusiasts have developed a so-called 30-30-30 rule when the hard reset router helps bring any router back to its original default settings.
-

40/30/20/10 Rule: The most scientific time management method
in addition to the 80/20 rule - one of the gold standards applied in all areas of life, the 40-30-20-10 rule is also a rule adopted by many people to manage the most scientific time.
-

Controlling Internet Access: Introduction to TMG Access Rule - Part 2
in the second part of this article series, i will show you the details of access rules after working together to create a rule using the wizard in part 1.
-

Controlling Internet access - Part 4: TMG Network and Network Rule
in the next part of this article series, i will show you some of the concepts used in the tmg firewall network - tmg firewall network and tmg firewall network rule.
-

Rule 10/10/10 helps you to regain your morale after the sadness that seems like you want to die
time is a miracle remedy to relieve all pain. this 10/10/10 rule will be helpful for those who are experiencing life problems.
-

Have you ever wondered why we count to 3?
have you ever wondered why we count to 3? let's find out in the article below!
-

Controlling Internet Access: Introduction to TMG Access Rule - Part 1
in this series, i will show you some of the basics of access rules for managing the new tmg firewall.
-

How to export or back up Windows Firewall rules
when you configure the firewall, it is important that you back up all windows firewall rules for safety and security. in this quick guide, tipsmake.com will show you the steps to back up windows firewall rules in windows 10.
-

Create a Rule to move and store email to another folder in Outlook
if multiple emails are received from the same sender every day, why not create a separate folder for that address.
-

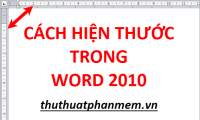
How to show the ruler in Word 2010 and the rule bar in Word 2010
how to show the ruler in word 2010, the rule bar in word 2010. in the process of working with word 2010, you accidentally see the vertical ruler and the horizontal ruler, also known as the ruler bar. you are not sure how to display two ruler bars to c
-

Controlling Internet Access: Introduction to TMG Access Rule - Part 3
in the third part of the introductory series of tmg access rules, i will introduce you to the basics of web publishing rules.
-

How to create a folder in Outlook 2016 using the rule
do you often receive emails in outlook from a specific colleague or customer and want to automatically transfer those emails to a different inbox folder for easy search? read this article to learn how to create an email transfer folder in outlook 2016 using the rule.
-

Algorithm for sharing (divide and conquer)
divide and conquer (divide and conquer) is an important method of designing algorithms. the idea of this method is quite simple and very easy to understand.
-

How to create a folder in Outlook 2013 by creating a rule
by default, outlook receives all incoming email and transfers it to the inbox folder. some people find it difficult to find messages in inbox and want to set up to automatically transfer certain emails to another folder to make it easier to find. this article will show you how to create a rule in
-

How to display rules in Word 2013 and 2016 - How to display rule bars in Word 2013 and 2016
how to show the ruler in word 2013 and 2016 - how to display the rule bar in word 2013 and 2016. you use word 2013 and 2016 to edit documents, but in the process of working, you do not see the vertical and horizontal ruler. . and you guys don't know how to hi yet
-

The 5-finger rule, teaching children to avoid sexual abuse, should all parents know
just five minutes, the mother was able to teach her to protect herself against the risks of abuse with a very simple and easy-to-remember rule.
-

Overview of Windows Server 2008 Firewall with advanced security features (continued part 3)
in this article, i will show you how to create an ipsec isolation domain policy in a simple network, create a quarantine domain rule for servers and clients that require security (authentication), configure the server to use ping connections sent to them to check the newly created rule.
-

5-hour rule: The secret of success of celebrities
spending at least 5 hours a week on purposeful training is the secret to benjamin franklin, oprah winfrey, elon musk, mark zuckerberg or bill gates achieving success that makes the world admire.
-

It's easy to lock your personal Facebook account without using your real name
facebook's rule is to use the real name when registering a personal account, but many vietnamese people often do not comply with this rule, resulting in a blocked or lost account.