malicious software
-
 Hackers Use Malicious Google Ads to Steal Users' Microsoft Accounts
there is a dangerous trend being deployed by the global hacker community, which is abusing the google ads platform to spread malicious code.
Hackers Use Malicious Google Ads to Steal Users' Microsoft Accounts
there is a dangerous trend being deployed by the global hacker community, which is abusing the google ads platform to spread malicious code.
-
 7 signs your computer is infected with malware
users should be wary of malware if they see too many pop-up pages appearing or some customizations suddenly changing.
7 signs your computer is infected with malware
users should be wary of malware if they see too many pop-up pages appearing or some customizations suddenly changing.
-
 Dirty SEO campaign brings a series of malicious software to the top of search
cybercriminals are using dirty seo methods to bring malicious software to the top of search.
Dirty SEO campaign brings a series of malicious software to the top of search
cybercriminals are using dirty seo methods to bring malicious software to the top of search.
-
 STOP - Ransomware is the most active in the Internet but rarely talked about
the fight against stop ransomware in particular and other ransomware strains in general is still very difficult and no appointment of an end date.
STOP - Ransomware is the most active in the Internet but rarely talked about
the fight against stop ransomware in particular and other ransomware strains in general is still very difficult and no appointment of an end date.
-
 Agent Smith code is threatening 25 million Android devices
yesterday, july 10, cybersecurity agencies issued a warning about a malicious software called agent smith that is causing about 25 million android phones to be affected.
Agent Smith code is threatening 25 million Android devices
yesterday, july 10, cybersecurity agencies issued a warning about a malicious software called agent smith that is causing about 25 million android phones to be affected.
-
 How does malware target illegal streams?
illegal torrents have been the number one enemy for producers and movie theaters. however, time is changing everything. today, users are switching to streaming movies instead of torrent them.
How does malware target illegal streams?
illegal torrents have been the number one enemy for producers and movie theaters. however, time is changing everything. today, users are switching to streaming movies instead of torrent them.
-
 How to identify computers infected with viruses with 10 characteristic signs
no one wants to own a computer infected with the virus. how can i know if my computer has a virus? in fact, there are some signs that help you identify the presence of malware in your computer, let's find out.
How to identify computers infected with viruses with 10 characteristic signs
no one wants to own a computer infected with the virus. how can i know if my computer has a virus? in fact, there are some signs that help you identify the presence of malware in your computer, let's find out.
-
 New discovery of the first version of Stuxnet malicious code
on the afternoon of february 27, 2013, symantec announced in vietnam the new version of the stuxnet malware version, and said that the stuxnet project could be launched in 2005 instead of 2009 as announced. before.
New discovery of the first version of Stuxnet malicious code
on the afternoon of february 27, 2013, symantec announced in vietnam the new version of the stuxnet malware version, and said that the stuxnet project could be launched in 2005 instead of 2009 as announced. before.
-
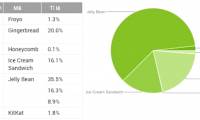
 Android operating system is the top target of hackers
99% of mobile attacks are targeted at android but many devices running this operating system are not updated to the latest version to fix the error.
Android operating system is the top target of hackers
99% of mobile attacks are targeted at android but many devices running this operating system are not updated to the latest version to fix the error.
-
 Chrome OS cannot pass the Android shadow yet
this month, the it community stirred up when google suddenly tested the cr-48 laptop model with the pre-installed chrome os.
Chrome OS cannot pass the Android shadow yet
this month, the it community stirred up when google suddenly tested the cr-48 laptop model with the pre-installed chrome os.
-
 Top 10 most dangerous malware types with bank accounts
zeus, spyeye, ice ix or citadel are notorious malware software that can infiltrate user computers, poison and steal personal information and financial data on online bank accounts. online.
Top 10 most dangerous malware types with bank accounts
zeus, spyeye, ice ix or citadel are notorious malware software that can infiltrate user computers, poison and steal personal information and financial data on online bank accounts. online.
-
 Strange ransomware detection only attacks the rich
other ransomware often spread to all victims if possible, but the new ransomware is different, it selectively infects.
Strange ransomware detection only attacks the rich
other ransomware often spread to all victims if possible, but the new ransomware is different, it selectively infects.
 Hackers Use Malicious Google Ads to Steal Users' Microsoft Accounts
there is a dangerous trend being deployed by the global hacker community, which is abusing the google ads platform to spread malicious code.
Hackers Use Malicious Google Ads to Steal Users' Microsoft Accounts
there is a dangerous trend being deployed by the global hacker community, which is abusing the google ads platform to spread malicious code.
 7 signs your computer is infected with malware
users should be wary of malware if they see too many pop-up pages appearing or some customizations suddenly changing.
7 signs your computer is infected with malware
users should be wary of malware if they see too many pop-up pages appearing or some customizations suddenly changing.
 Dirty SEO campaign brings a series of malicious software to the top of search
cybercriminals are using dirty seo methods to bring malicious software to the top of search.
Dirty SEO campaign brings a series of malicious software to the top of search
cybercriminals are using dirty seo methods to bring malicious software to the top of search.
 STOP - Ransomware is the most active in the Internet but rarely talked about
the fight against stop ransomware in particular and other ransomware strains in general is still very difficult and no appointment of an end date.
STOP - Ransomware is the most active in the Internet but rarely talked about
the fight against stop ransomware in particular and other ransomware strains in general is still very difficult and no appointment of an end date.
 Agent Smith code is threatening 25 million Android devices
yesterday, july 10, cybersecurity agencies issued a warning about a malicious software called agent smith that is causing about 25 million android phones to be affected.
Agent Smith code is threatening 25 million Android devices
yesterday, july 10, cybersecurity agencies issued a warning about a malicious software called agent smith that is causing about 25 million android phones to be affected.
 How does malware target illegal streams?
illegal torrents have been the number one enemy for producers and movie theaters. however, time is changing everything. today, users are switching to streaming movies instead of torrent them.
How does malware target illegal streams?
illegal torrents have been the number one enemy for producers and movie theaters. however, time is changing everything. today, users are switching to streaming movies instead of torrent them.
 How to identify computers infected with viruses with 10 characteristic signs
no one wants to own a computer infected with the virus. how can i know if my computer has a virus? in fact, there are some signs that help you identify the presence of malware in your computer, let's find out.
How to identify computers infected with viruses with 10 characteristic signs
no one wants to own a computer infected with the virus. how can i know if my computer has a virus? in fact, there are some signs that help you identify the presence of malware in your computer, let's find out.
 New discovery of the first version of Stuxnet malicious code
on the afternoon of february 27, 2013, symantec announced in vietnam the new version of the stuxnet malware version, and said that the stuxnet project could be launched in 2005 instead of 2009 as announced. before.
New discovery of the first version of Stuxnet malicious code
on the afternoon of february 27, 2013, symantec announced in vietnam the new version of the stuxnet malware version, and said that the stuxnet project could be launched in 2005 instead of 2009 as announced. before.
 Android operating system is the top target of hackers
99% of mobile attacks are targeted at android but many devices running this operating system are not updated to the latest version to fix the error.
Android operating system is the top target of hackers
99% of mobile attacks are targeted at android but many devices running this operating system are not updated to the latest version to fix the error.
 Chrome OS cannot pass the Android shadow yet
this month, the it community stirred up when google suddenly tested the cr-48 laptop model with the pre-installed chrome os.
Chrome OS cannot pass the Android shadow yet
this month, the it community stirred up when google suddenly tested the cr-48 laptop model with the pre-installed chrome os.
 Top 10 most dangerous malware types with bank accounts
zeus, spyeye, ice ix or citadel are notorious malware software that can infiltrate user computers, poison and steal personal information and financial data on online bank accounts. online.
Top 10 most dangerous malware types with bank accounts
zeus, spyeye, ice ix or citadel are notorious malware software that can infiltrate user computers, poison and steal personal information and financial data on online bank accounts. online.
 Strange ransomware detection only attacks the rich
other ransomware often spread to all victims if possible, but the new ransomware is different, it selectively infects.
Strange ransomware detection only attacks the rich
other ransomware often spread to all victims if possible, but the new ransomware is different, it selectively infects.