Article on the subject of "cyberattack"
-

Microsoft revealed the 'system crash' incident in early June was caused by a DDoS attack
during the first week of june, microsoft unexpectedly experienced a severe outage affecting most of its services including azure, outlook, and teams.
-

FBI Begins Investigation of a Serious Internal Cybersecurity Incident
the us federal bureau of investigation (fbi) is said to be conducting a comprehensive investigation into all malicious cyber activity taking place on the agency's internal network.
-

Detecting a new strain of malicious code that abuses Windows Installer to deploy infection activities
security researchers at red canary have discovered a new windows malware capable of spreading by means of an external usb drive. this malware is associated with an agent group called raspberry robin, which was first observed in september 2021.
-

Detected malicious attack campaign targeting TikTok, threatening to delete accounts of many celebrities
international security researchers have recently issued an urgent warning about a new phishing attack campaign on the tiktok platform.
-

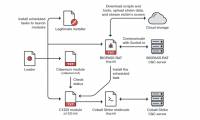
Beware of BIOPASS malware hidden in Chinese online gambling sites
cybersecurity researchers are warning of a new malware - biopass rat - attacking online gambling companies in china.
-

Hackers can spy on Samsung users with pre-installed apps
sergey toshin - founder of oversecure company specializing in mobile application security, has found more than a dozen vulnerabilities affecting samsung devices, allowing hackers to steal information and track users.
-

Warning: Microsoft and Google Clouds are being abused to launch large-scale phishing campaigns
statistical results show that in the first quarter of 2021 alone, global criminals sent 52 million malicious messages by abusing well-known storage services such as office 365, azure, onedrive, sharepoint. , g suite and firebase.
-

Kaspersky accused the APT32 hacker group of using the Google Play Store to spread spyware for years
kaspersky security researchers found a malicious campaign called phantomlance targeting android device users.
-

What types of data are for sale on the dark web?
what are the most popular types of data for sale on the dark web?
-

Anxiety, depression and psychological trauma: The invisible effects caused by cybercrime
we have long judged the severity of a cyber security disaster through financial losses and forgetting of negative mental consequences.
-

What is this year's annual cyber security report?
ibm has released its annual cybersecurity report x-force threat intelligence index. this is one of the largest and most reputable reports in the field of security.
-

The flaw in the ICS system - the grave of the business
enterprises are the favorite target of malicious agents on cyberspace.
-

Why must India implement security systems for the power sector?
recently, the indian power business association has come to an agreement that it will deploy a comprehensive firewall system, combined with many other security measures.
-

Media giant Nikkei was cheated and lost $ 29 million
media giant nikkei suffered losses of up to $ 29 million.
-

Discovering a large-scale APT attack into Vietnam, users need to quickly download the malicious tool
the department of information security recommends that users urgently download this malicious code-checking and removal tool on ais.gov.vn; vncert.vn was built and provided by the department.
-

Cyber-Attack attacked the US military network
after the us army strategic command issued a ban on the use of mobile communications devices in the us military network last week ...
-

CMC InfoSec provides malware removal tool for online DDoS attack
your computer may be infected with cbot malicious code and is one of the tens of thousands of 'militants' that are attacked by attackers taking advantage of ddos attack on vietnamese websites these days. however, there were tools to destroy this dangerous malicious code.
-

Security researcher identified Sharpshooter spy attacks related to the Korean hacker group
the finding comes through new evidence collected by researchers after analyzing a command and control server (command-and-control server - c2).
-

Network security researcher claims to find a way to decode WannaCry
ransomware wannacry has infected hundreds of thousands of computers around the world. recently, a cyber security researcher said he had found a way to defeat it.
-

McAfee expert explained how deepfake and AI are drilling through the cyber security wall
'hundred listeners are not equal to one', this proverb might not be accurate when it comes to cyber security.
-

Anxiety, depression and psychological trauma: The invisible effects caused by cybercrime
we have long judged the severity of a cyber security disaster through financial losses and forgetting of negative mental consequences.
-

What is extortionware? How is it different from Ransomware?
malware comes in many different forms. a particularly worrying example is extortionware, a term that covers many types of cyberattack software.
-

The Cryptojacking problem in Southeast Asia fell 78% after INTERPOL intervened
cryptojacking is an emerging form of cyberattack, associated with the development of cryptocurrencies.
-

The UN acknowledges that cyberattacks are extremely sophisticated and cannot identify the culprit
the united nations recently acknowledged the organization was the target of a massive cyberattack in the summer of 2019.
-

DeepSeek hit by cyberattack, new registrations restricted
deepseek said on monday it would temporarily restrict new user registrations 'due to large-scale malicious attacks'.
-

McAfee expert explained how deepfake and AI are drilling through the cyber security wall
'hundred listeners are not equal to one', this proverb might not be accurate when it comes to cyber security.
-

Network security researcher claims to find a way to decode WannaCry
ransomware wannacry has infected hundreds of thousands of computers around the world. recently, a cyber security researcher said he had found a way to defeat it.
-

The flaw in the ICS system - the grave of the business
enterprises are the favorite target of malicious agents on cyberspace.
-

Hacker successfully stole 100,000 photos from border control database
the us customs and border protection department officially released a statement on monday that the database of one of their subcontractors was 'visited' by hackers in a malicious cyberattack.
-

Microsoft revealed the 'system crash' incident in early June was caused by a DDoS attack
during the first week of june, microsoft unexpectedly experienced a severe outage affecting most of its services including azure, outlook, and teams.
-

Detected malicious attack campaign targeting TikTok, threatening to delete accounts of many celebrities
international security researchers have recently issued an urgent warning about a new phishing attack campaign on the tiktok platform.
-

The conclusion for hackers stole 114,000 iPad accounts
eventually the culprit of the at&t cyberattack also bowed to the guilty plea after being arrested earlier this year, claiming ways to take away 114,000 ipad users' accounts.
-

Warning: Microsoft and Google Clouds are being abused to launch large-scale phishing campaigns
statistical results show that in the first quarter of 2021 alone, global criminals sent 52 million malicious messages by abusing well-known storage services such as office 365, azure, onedrive, sharepoint. , g suite and firebase.
-

Beware of the 'Windows 11 Alpha' cyberattack campaign
taking advantage of the interest of users, cybercriminals are deploying windows 11-themed phishing campaigns.
-

Beware of BIOPASS malware hidden in Chinese online gambling sites
cybersecurity researchers are warning of a new malware - biopass rat - attacking online gambling companies in china.
-

Google warns hackers are abusing Gemini to accelerate cyberattacks.
google says that state-backed hacking groups are using gemini to accelerate cyberattacks, from target research to vulnerability exploitation.
-

What types of data are for sale on the dark web?
what are the most popular types of data for sale on the dark web?
-

Smishing, public WiFi, deepfake ... but every security threat will explode in 2020
the world of security is constantly moving, in parallel with the development speed of the internet as well as the technology field.
-

FBI Begins Investigation of a Serious Internal Cybersecurity Incident
the us federal bureau of investigation (fbi) is said to be conducting a comprehensive investigation into all malicious cyber activity taking place on the agency's internal network.
-

This malware was written in an unusual programming language, making it extremely difficult to detect
international cybersecurity researchers have discovered a relatively popular cyberattack campaign that is actively spreading a new type of malware. it is worth mentioning that this malicious code is written in a rather strange programming language, very rarely used to compile malicious code.