software vulnerabilities
-

Bulgaria: Getting urgent IT experts for revealing vulnerabilities in software
petko petrov - a famous it expert - was arrested on charges of arbitrarily exploiting and disclosing information about the security vulnerability of the software system used by local kindergartens. -

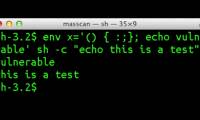
Safeguard against Shellshock security vulnerabilities
the main advice for computer users is to always check for the latest software updates as soon as possible. -

Sorry, Kaspersky, Microsoft is building more security tools in Windows 10 Fall Creators Update
security is becoming a central issue for microsoft, and in a way, it is also a factor that brings many new things to windows 10, such as windows store, os 10 or windows 10 s.