Article on the subject of "wireless network"
-

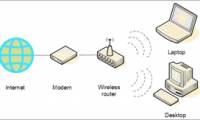
The process of setting up a wireless network
the process of setting up a wireless network will basically be like. that is the topic in this article that we will introduce you to the process of setting up a wireless network.
-

Guide to building an Ultimate Wireless Network
let's take a look at what you need to know to select a wireless router, configure a network and start working.
-

Upgrade Wi-Fi security from WEP to WPA2
we already know that wep security is very easy to crack, this security technology only protects your wireless network from ordinary users. also, for hackers, even new hackers can download free tools and follow some instructions to crack your wep key.
-

Network security guide before vulnerability 196
first we need to understand the attacks using this vulnerability must be done within the network. the culprit must have network certificates and need to have a successful connection to your network.
-

Wi-Fi Enterprise and 802.1X encryption in Mac OS X
in this tutorial, i will show you how to configure and connect wpa / wpa2-enterprise networks in leopard and 10.6 snow leopard.
-

Secure the wireless network at the packet level
in this article, i will show you some useful techniques for troubleshooting wireless network security issues at the packet level.
-

Install laptop to prioritize wired network connection
have you ever been in a situation where, even though you connected your laptop to a wired network, the device still sees the previous wireless network as the default connection? the article will show you how to fix this problem quickly and easily.
-

How to use Command Prompt to manage wireless networks on Windows 10?
to manage the wireless network connection on a windows 10 computer, you can use the settings or control panel applications. however, there are many advanced settings that you cannot find on the settings application or on the control panel. in this case you can use command prompt.
-

What is 4 x 4 MIMO? Is your phone needed?
mimo stands for 'multiple input, multiple output'.
-

Why do you need to learn about IEEE 802.11ax?
why should you care about ieee 802.11ax? please join tipsmake.com to find out the draft ieee 802.11ax standard for scope, throughput and stability in this article!
-

Learn SSID and wireless network
the ssid (short for service set identifier) is the primary name associated with 802.11 wireless lan (wlan) including home and public hotspots. client devices use this name to identify and connect to a wireless network.
-

Instructions on how to install DD-WRT
are you frustrated by software limitations on your router? go ahead and replace that software with dd-wrt software provided by linux.
-

Chrome OS cannot pass the Android shadow yet
this month, the it community stirred up when google suddenly tested the cr-48 laptop model with the pre-installed chrome os.
-

Instructions for accessing the Internet via phone running Android
not everyone knows this: users can share their android mobile phone internet connection with other devices via wifi. this feature is called a tether, or turns the phone into a transmitter modem. most mobile operators in the us charge extra tether fees, or not accept the contract feature.
-

The 5G network in Korea is capable of downloading 800MB of data in 1 second
the 4g lte-advanced 3-band network has not yet been officially launched, but south korea has considered widening the road for 5g.
-

Wi-fi router applications to accurately track and identify all your actions
the researchers found a way to use a wi-fi router to track people - very accurately.
-

Wi-Fi 6, how will the next Wi-Fi version change the concept of wireless networks?
the next wi-fi version will be called wi-fi 6, not a technical name like 802.11ab or 802.11n.
-

Quiz: What causes Wifi network slow?
with the continuous development of technology, the use of wireless networks is becoming more and more popular. however, connecting to the internet using wi-fi is not always easy, especially if the speed of access may be severely reduced despite the use of strong connections. find out about some of
-

Wireless network knowledge test
this term test is knowledge of wireless network. these are just the most basic knowledge you must know when researching wireless networks
-

Facebook partnered with Qualcomm for high-speed wireless Internet
facebook has just put qualcomm on the wifi gigabit terragraph project collaboration list.
-

Learn about Wireless Sensor Network (WSN)
wireless sensor network (wsn) is an infrastructure-free wireless network that is deployed with a large number of wireless sensors in a special way that is used to monitor the system, physical condition or the environment.
-

Basic guide: wireless network - Wireless
this article shows you how to set up or 'tune' your wireless network, then connect more printers, music players, and tvs to this wireless network.
-

Learn SSID and wireless network
the ssid (short for service set identifier) is the primary name associated with 802.11 wireless lan (wlan) including home and public hotspots. client devices use this name to identify and connect to a wireless network.
-

Basically about Wireless Networking
wireless networking (wireless networking) is a new solution for office, home, or large network models where ethernet networks cannot work. installing a basic wireless network is simpler than the ethernet (wired network) network, and you can easily import more pcs or other devices to the network.
-

Learn about basic WLAN devices
wireless network (wireless local area network) is the preferred wireless network system by providing high-speed data transmission, with long distances without worrying about wires, cables ...
-

4 steps to set up your home wireless network
you can use the wireless network to share internet access, files, printers ... or you can use it to surf the web even when you're sitting in bed or in the garden.
-

Upgrade wireless network system
common universal wi-fi network is not chosen by enterprise (dn) as the main means of connection ...
-

Wireless LAN security (Term 2)
a wireless lan consists of three parts: wireless client, access points and access server. the typical wireless client is a laptop with a wireless nic (network interface card) installed to allow access to the wireless network. access points (ap) provide three
-

Several ways to improve Wi-Fi connection
wi-fi wireless network is one of the biggest utilities of using a laptop instead of bulky desktops. instead of having to sit around all the time to keep away from the range of the network, you can carry your laptop across the room and still be able to surf the web comfortably.
-

4 tips for building better wireless networks
how much performance do companies want to implement when they deploy a wireless network? these cases may not be enough - especially when wireless becomes a key part of the new data center infrastructure.
-

How to turn on / off automatically wireless network connection in Windows 10
when you connect to a new wireless network, windows creates a profile for that wireless network. this guide will show you various ways to enable or disable the automatic connection to wireless networks in windows 10.
-

Upgrade wireless network security
do you think the wireless network i am using is really safe? it is better to reconsider this issue. the latest wi-fi security standard, called wireless protected access 2 (wpa2), adds specialized data encryption capabilities.
-

Guide to DD-WRT - Part 2: Extending scope with WDS
a wireless distribution system (wireless distribution system), is an economical and easy solution that can extend the coverage of wireless networks.
-

Set up a wireless home network with 4 basic steps
you can design for yourself a simple wireless network, to share internet access, files, printers ... you can surf the net while you are in the yard, or in the garden ... to set up a wireless computer network is quite simple, you just need to do it in 4 steps:
-

Basic knowledge to set up a home wireless network
this article will show you how to perform step-by-step programs: plan, build, and test a home wireless network. although many typical wireless networks have made incredible strides in
-

What is WBAN (Wireless Body Area Network)?
the term 'wireless body area network' was coined in 2001 by van dam. it is essentially a network of sensor nodes attached to the human body, used to measure human biological signals (heart rate, blood pressure, brain signals, etc.). .
-

Secure the wireless network at the packet level
in this article, i will show you some useful techniques for troubleshooting wireless network security issues at the packet level.
-

Set up Ad Hoc wireless network to play WiFi without software from your laptop
creating ad hoc wireless networks is simple and easy, it will take you less than a minute to create ad hoc wireless networks on your laptop. but before doing wifi sharing with ad hoc, you should know what this ad hoc wireless network feature is and which laptop can create ad hoc?
-

How to be safe on a wireless network
most people enjoy the benefits of wireless technology. wireless networks obviously bring many advantages to users, and they can be vulnerable if you don't have security.
-

DD-WRT Guide - Part 3: Building a Wireless Bridge
network connectivity is emerging more and more in non-traditional electronic devices, including digital music players, digital cameras, printers ...