Article on the subject of "systems"
-

Use vSphere Hot-Add to adjust CPU and RAM
for those who often have to use and work in virtual environments, the shortage of hardware resources occurs quite a lot. however, if they want to fix this problem, how will they do it? pause the program, upgrade the system ... in the following article, we will guide you some basic tasks to limit.
-

Delete log information in Windows Server Backup
windows server backup is one of windows server 2008 / r2's useful features that allows users to easily back up, restore files, data and other important components in the system like system state, full server or the entire hard drive according to user needs. after such processes, windows server
-

Configure Cisco ASA system with Android, VPN and Active Directory Authentication devices
in the following article, we will cover some basic operations to configure and set up cisco asa systems with devices based on android, vpn operating system and active directory authentication.
-

Ultra-fast data recovery solution
today (april 15), the world's leading security solutions provider - symantec has officially announced its strategy to help businesses solve data recovery and system challenges in the shortest time. .
-

Track changes in sensitive security in Windows
attack surface analyzer is a tool released by microsoft that allows users to easily detect sensitive security changes of the windows operating system.
-

Security in virtualization and worrying things
in a conference of it industry leaders in march, it managers expressed their concerns about the security of virtual infrastructure.
-

Determine which system is attacked by Windows commands
in this two-part tutorial, the first part will cover five useful command-line tools in windows to perform such an analysis.
-

The world is at risk of virtual war
security experts believe that the stuxnet virus, infiltrating some computers in iran's nuclear program, is part of a darker plan: to start an online war.
-

Find out about Virus.Win32.Sality.ag template
viruses like these often have a mechanism to replicate the resources on the infected computer, unlike worms, unused viruses and exploit network services to replicate and spread themselves to other computers ..
-

Enable Hyper-V Manager mode in Windows 8
as we know, the 'birth' of windows 8 has led to a lot of changes in how people manage and work. technically, windows 8 has built-in functionality to manage microsoft virtualization and hypervisor for experienced users, so they won't need to switch to windows 8 server to use hyper-v. client
-

Learn about the management and monitoring functions of Resource Monitor tool
in the following article, we will show you some of the features and usage of the handy resource monitor tool from microsoft, which is used to manage and monitor the operation of the network system. storage capacity and system performance ...
-

Learn about WebMatrix - part 2
in the next part of the technical article series on webmatrix, we will learn about components such as using layout, data, and pages that create data ...
-

Top 100 free apps for Mac OS X
in the following article, tipsmake.com will share with you the list of top 100 most popular free apps for mac os x ...
-

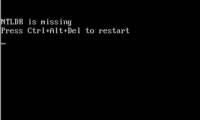
Common computer errors and remedies (Part 2)
let's continue to review common errors when using computers and ways to solve them.
-

10 secret features of Mac OS X Lion
apple's new operating system - mac os x lion has officially appeared, bringing a new wind to the apple community and using apple technology, as well as a host of new features that have never been known. although users can find out by themselves at the official website of the company, but it seems
-

Experience with K7 application - Total Security 11.1
the name k7 may be unfamiliar to many users, but in the security software market today, this application has a fairly solid foothold. from 1991 until now, they have focused on building and developing security solutions, helping computer users avoid the common troubles in today's life ...
-

Instructions to encrypt and 'hide' BitTorrent traffic data
through the previous analysis articles on tipsmake.com, we understand the basics of bittorrent as a form of storing and sharing files and data online. besides, the transmission and sharing of unallocated files and data is a contradictory form, for example when we use and download files from a fixed
-

4 useful tools for online web editing
in the following article, we will introduce you some online editing tools that are quite diverse and useful for web development. these applications have a common feature that can work on a variety of environments, in any condition, as long as there is an internet connection.
-

6 utilities needed to improve Microsoft Office performance
anyone who has ever used microsoft's office suite agrees with two things: these applications have changed the way everyone works - especially office workers, second is needed. there must be changes to improve office features ...
-

Download and backup data of Google, Google Plus
up to this point, google has provided users with a wide range of utility services to help them maximize their performance and save a lot of time compared to the past. but do users think about the risk of not being able to access the account or worse, losing the data ...
-

How to Be a Systems Administrator
today's workplace relies on computer systems. without computers and networks, we would be unable to communicate or even complete very basic tasks – we would be paralyzed. systems administrators keep the modern workplace going by m...
-

How to Become a System Analyst
systems analysts analyze and improve the efficiency and productivity of businesses' it systems and networks. in order to be able to do the job, a systems analyst needs a strong background in computer and business-related fields. teamwork,...
-

Intrusion detection system (IDS) (Part 1)
ids (intrusion detection systems) is a device or software that monitors network traffic, suspicious behaviors and alerts for system administrators.
-

What test do you know about the operating system (Part 1)
in the following article, please join the network administrator to learn about the operating system through extremely interesting multiple choice questions. let's start.
-

What test you know about operating system P6
the operating system is an important and necessary software for any mobile device or laptop. to help readers find out more about this topic, the quiz below network administrators have compiled and sent you.
-

What test do you know about P2 operating system?
in this next section, let's join the network administrator to continue learning about the operating system through extremely interesting multiple choice questions.
-

What test you know about operating system P5
the set of multiple-choice questions on the operating system of the network administrator hopes to provide you with a lot of useful knowledge. invite your reference.
-

The incompatibility of the systems in Pokemon GO
when playing pokemon go, players need to pay attention to the problem of the conflicting systems to ensure their victory when fighting other pokemon. this article will provide you with the full conflicting systems of different pokemon, helping you ensure victory.
-

What test you know about operating system P11
please read your knowledge and the following multiple choice questions of network administrator. hope with these questions will give you lots of useful information.
-

What test you know about operating system P7
please read your knowledge through multiple choice questions around the operating system topic. the question set will have 10 sentences to try.
-

What test you know about operating system P4
operating system is a term that is no longer strange to users on mobile devices or computers. in the article below, invite readers to try the multiple choice questions about the operating system of the network administrator.
-

Some notes before choosing to buy a laptop
laptop systems are becoming increasingly popular due to the rapid increase in performance and mobility. many systems today are being marketed to replace desktop systems, but only a few can do so.
-

Interesting operating systems may be unknown to you
in addition to the usual operating systems such as windows, mac os or linux, there are many other operating systems suitable for many different uses. here are 8 interesting operating systems that you may not know yet.
-

What test you know about operating system P12
you love to learn the knowledge about the operating system. if you feel depressed when reading long articles, try the following multiple choice questions of network administrator. there are many good quizzes to learn.
-

What test you know about operating system P13
a set of multiple-choice operating system questions that help readers re-examine their knowledge and contribute positively to your work. the set of questions consists of 15 sentences with many different topics, invite readers to try.
-

What test you know about operating system P9
in previous posts network administrator has sent you to read the operating system questions to help you test your knowledge on this topic. the next section will continue to be multiple choice questions about the operating system. invite your reference.
-

What test you know about operating system P10
in previous posts network administrator has sent you to read the operating system questions to help you test your knowledge on this topic. the next section will continue to be operating system multiple-choice questions for your reference.
-

What test you know about the P8 operating system
you are learning about computer or mobile operating system. if you feel tired of reading lengthy articles, the multiple choice questions below will help you feel more excited. the following network administrator will send you a series of articles revolving around this topic.
-

10 operating systems for security research preferred by hackers
here is a list of 10 computer operating systems used by hackers worldwide, please refer.
-

What test you know about operating system P3
please read the test questions about the operating system below. in this section, there will be 10 questions, please see and choose the best answer.