Article on the subject of "user information"
-

Australia sued Facebook for privacy violations, claiming up to $ 529 billion
the australian government will sue facebook for up to $ 529 billion in damages. this amount is even more than the amount the government of this country collected within a year.
-

Windows User State Virtualization - Part 4: Complex environment
in the next part of this series, we will discuss the considerations and strategies for implementing usv in complex environments.
-

Windows User State Virtualization - Part 5: Complex environment
in this section, we will show you the high-level steps for implementing various windows user state virtualization solutions.
-

Windows User State Virtualization - Part 2: Scenario
in part 2 of this series, we will explore different business scenarios for implementing windows user state virtualization technologies (usv.
-

Windows User State Virtualization - Part 3: Virtualizing application state
in the third part of this series, we will show you how to manage the appdataroaming folder when virtualizing application settings and data.
-

Windows User State Virtualization - Part 1: Technology and some problems
in this article we will introduce you to the windows user state virtualization technologies (usv) as well as discuss some issues when planning a usv strategy.
-

Virus encrypts victim's computer data for ransom
the uk crime prevention agency (nca) in november issued a warning about a virus that is spreading very fast online via email, called crytolocker.
-

How to delete search history on Facebook?
facebook has recorded everything that users search from the facebook website. so, how to delete that archive list, or how to limit user information that facebook can host?
-

Security experts discovered that the line appropriated bank accounts, Facebook, Gmail ... very large in Vietnam, you can also be a victim
many types of accounts, from bank accounts to website administration accounts.
-

Facebook users will not be able to avoid being tracked and collected for advertising purposes
there is no way for people to refuse facebook's use of their information for advertising, a facebook spokesman told gizmodo.
-

Why is your data worthwhile?
user data is what companies want, organizations want, government wants or even some individuals want, and indeed user data is worth it.
-

Keep important information
today computers are more interconnected than before, internet applications become smarter and more advanced, they are built into applications that can collect user information. this information is
-

The way Facebook collects user information even without an account
facebook has posted an article describing more clearly how they saved some user information even when they logged out or not registered members on facebook.
-

More than 4,000 Android apps reveal user information
according to thehackernew, the entire android application uses google's firebase cloud service and it is unclear what causes the user's sensitive information to be exposed.
-

How to change the browser User Agent without extenstion
if you want to make your web traffic seem to come from another browser, you can do it. all popular browsers offer a built-in user agent converter, so you can change it without installing any extensions.
-

How valuable is the user's personal data?
personal information obtained by users after theft or unauthorized data access becomes a commodity and is bustling on dark web (underground web), a huge market of stolen data and information.
-

Apple does not sell user information!
a study of security scale has shown that apple's ios operating system contains underground tools, allowing governments and other organizations to gather information from iphone, ipad and ipod devices without for known users.
-

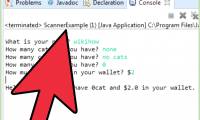
How to Get Input from a User in Java
when programming in java or any other language, you will most likely need to use input information from a user. java provides many different methods for getting in user information, but the most common and perhaps easiest to implement...
-

XML and information on demand
recently, we often hear the concept of 'information on demand.' information on demand is understood in the sense that the organization's information system must meet all user requirements, from leadership to professional staff; from statistical information, forecast to detailed information for
-

What is a cookie? How does cookie work?
a cookie is a piece of text that a web server can store on a user's hard drive. cookies allow a website to store information on a user's computer and then retrieve it. information pieces will be saved as name-value pairs (name-value).
-

6 secret links of Google are used to track and collect user information
google tracks and collects user personal information through services provided by the company. and here are 6 secret links that google uses for this purpose.
-

WhatsApp will not sell user information
as a messaging service, whatsapp has to put security first, while facebook parent company is too famous for advertising activities (collecting and sharing user information). this caused a small concern for hundreds of millions of whatsapp users.
-

Apple allows users to download all data on iPhone
users can download a backup copy of all information related to their apple account, including apple id profiles, app store downloads, icloud documents, itunes purchases and even applecare history.
-

CSS is so powerful that it is possible to get anonymous Facebook user information
several new additions to the web standard cascading style sheet (css) are so powerful that a security researcher has used them to decode anonymous people (de-anonymize).
-

AR and VR, the most advanced technologies in the world, but with unpredictable risks?
vr and ar are gradually becoming a trend of future development and increasingly useful in many different fields and services, including sports, education, health and many other professional professions but is there any potential risk attached? let's find out!
-

Manipulating a finger on the smartphone screen can also reveal the user's personal information
it may sound unbelievable, but researchers have recently announced the fact that how to swipe, pinch and touch the fingers on the phone screen can be used to track and steal user information.
-

Transfer from Linux Mail Server to Exchange Server 2007 (Part 3)
through the previous two sections we have created users, this article will switch to the user information section. using the new-mailbox command cannot add the information we have in the csv file.
-

Facebook corrected with a series of new regulations to protect users' information after the scandal blew away $ 100 billion
after the scandal of information leakage of about 87 million users, facebook has introduced new rules to protect information to regain user trust.
-

Protect user location information in IE 9 and Firefox 4
if you still wonder and don't understand why online news websites or advertisers can know your current location, upgrade your browser to ie 9 or firefox 4. ..
-

Find User in SQL Server
do any queries on sql server return all user created?