Google said it would reward a total of nearly $ 3 million for hackers who found weaknesses on Chrome OS.
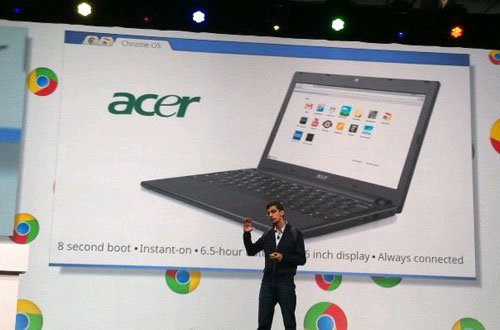
Google is actively promoting computers running Chrome OS
The world's number one search engine is scheduled to host a contest called ' Pwnium ' in March, when hackers will have the opportunity to test their skills by invading HP Chromebook 11 or Acer C720 machines. Chromebook , according to The Los Angeles Times .
Google said it would award a special prize worth $ 110,000 and $ 150,000 for successful attacks, with a total of nearly $ 3 million in prizes.
Any hackers who disable Chrome OS can receive a bonus of $ 110,000, while $ 150,000 is for attacks that take control of the computer even when the device is restarted.
" Pwnium " will take place during the CanSecWest security conference in Vancouver, Canada .