Ransomware InsaneCrypt or Everbe 1.0 is a ransomware family based on an open source project. This ransomware family is distributed through spam and hacked into Remote Desktop Services, but this is not yet confirmed.
The good news is that you can decode these ransomware variants for free using the decoder created by Michael Gillespie and Maxime Meignan. To use the decoder, the victim only needs to have an encrypted file and an unencrypted version of the same file. This can often be achieved through the templates provided by Windows.
Variations with the following extensions can be decoded with this tool.

.[email].insane .[email].DEUSCRYPT .[email].deuscrypt .[email].Tornado .[email].twist .[email].everbe .[email].embrace .[email].pain .[email].volcano
Unfortunately, this decoder will not decode their ransomware Everbe 2.0 variants because the version's encryption feature has no weaknesses to exploit.
How to decode ransomware InsaneCrypt and Everbe 1.0
The ransomware infection of InsaneCrypt or Everbe 1.0 can be determined by checking whether the files are encrypted and renamed to .insane, .DEUSCRYPT, .deuscrypt, .Tornado, .twist, .everbe,. pain, .volcano or .embrace or not.
To decrypt files encrypted by ransomware Everbe, first download the InsaneCrypt Decryptor tool here.
After downloading, just double click on the executable file to start decoding and you will be greeted with the main screen.

To decode, you need to import an encrypted file and its original unencrypted version. First, click the Settings menu and select Bruteforcer. This will open a screen where the user can select both the encrypted file and its unencrypted version as shown below.

After selecting both files, click the Start button to start decoding. This process may take a long time so be patient.

When finished, the decryption tool will indicate that the decryption key has been found. Now click the X button to close the BruteForcer window and the key will be loaded into the decoding tool as shown below.

Now, need to select a folder to decrypt. If you want to decrypt the entire drive, just select the drive letter itself. For example, in the image below, the author chose C: drive.
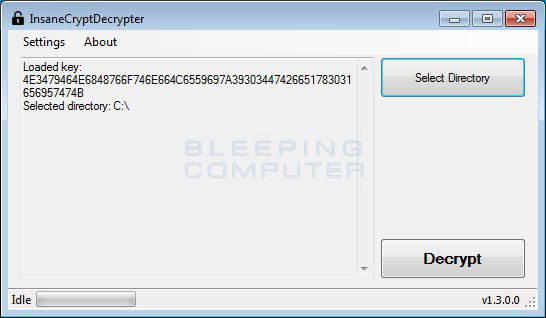
When ready, click on the Decrypt button to start decrypting files encrypted by ransomware Everbe. After clicking on the Decrypt button , the program will decrypt all encrypted files and display the decrypted status in the window.

When finished, the decryption tool will display a summary of the number of decoded files. If some files are ignored, it may be because of rights to those files.

Although the files are now decrypted, the original encrypted files will still be on the computer. When confirming that your files have been decoded correctly, you can use CryptoSearch to move all files encrypted by ransomware into a folder so that they can be deleted or stored.
Now you can close the decryption tool and use the computer as usual. If you need help using this decoder, please leave a comment in the comment section below!
Good luck!
See more:
- How to decode Stupid Ransomware with StupidDecrypter
- How to remove .bworm Files virus
- Completely remove Adware and Spyware on your system