Appeared malicious software 'clones' famous software
BitDefender - the leading provider of security solutions in the world has discovered and warned the return of famous brand clone software.
BitDefender, the world's leading provider of security solutions, has discovered and warned of the return of famous brand clone software .
The targeted 'bad' software this time is the Office ® 2010 Beta version. Just a week after the counterfeit software test of Windows 7, this time hackers launched a new fake Trojan, Office 2010.
The fake trojan hid under the shadow of Office 2010 is advertised on the Internet with very attractive titles to attract curious users to download. This malicious phishing product also promises to save users' time by attaching a beta version to the message as a compact zip file. This convenience makes many people eager to download and trap.
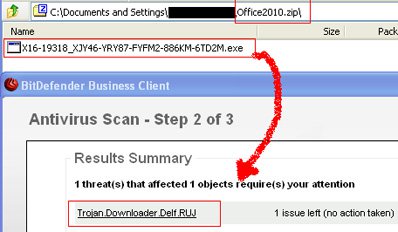
When extracting this file, security experts obtained an exe file named after the key to activate the Office® 2010 Beta version. BitDefender's global data security analysis identified it as Trojan.Downloader.Delf.RUJ , a malware running on a Windows platform designed to infiltrate a user's computer, secretly opening a path guide. When the 'entrance' is wide open, a large amount of adware and spyware will spill into your computer, creating countless popup ads.
After installation, the Trojan creates a copy of itself and modifies the registry to run the corresponding copies each time Windows starts. Then it tries to connect to an IP address to download other malicious files.Trojan.Downloader.Delf.RUJis becomes an extremely dangerous threat to personal data and financial data.
To ensure safety, BitDefender recommends that users download the software from the official vendor's website, not from unknown sites. Besides, an indispensable operation is to scan attachments with antivirus software strong enough before opening them.
- Dirty SEO campaign brings a series of malicious software to the top of search
- Appeared software can penetrate iCloud, Google Drive
- Top 10 most dangerous malicious codes in December 2006
- Risk of ransomware infection when downloading crack software online
- Learn and use the Windows Malicious Software Removal Tool
- A malicious extension 'occupies' Chrome and Firefox browsers appears, preventing users from uninstalling
- Appeared TikTok clones, pay video viewers, climbing to the top 1 App Store
- Warning with 4 dangerous variants of WannaCry malware
- Find bug in Emotet malware, prevent it from spreading for 6 months
- How to Make a Fake Picture With Famous People to Impress Your Friends and Family
- Top 10 'fake' laptops
- 107 new rootkit lines appeared in Vietnam within 30 days
- Warning of new malware appear like Wannacry, capable of deleting Vietnamese percussion on computer
- Warning: Appeared fake FaceApp application to install malicious code on users' devices