Article on the subject of "buffer overflow attack"
-

Techniques of exploiting buffer overflow errors - Part II
in the previous section we have reviewed the memory organization, stack, calling the function to understand thoroughly why when the buffer overflow occurs, we can change the value of the command pointer register% eip, from which can execute any code. we also learned how to create a simple shellcode
-

Techniques of exploiting buffer overflow errors - Part II
in the previous section we have reviewed the memory organization, stack, calling the function to understand thoroughly why when the buffer overflow occurs, we can change the value of the command pointer register% eip, from which can execute any code. we also learned how to create a simple shellcode
-

What is Buffer Overflow? Its Common Attack Types
buffer overflow, also known as buffer overflow, is a programming error that occurs when a program attempts to write data that exceeds the memory capacity allocated to a buffer.
-

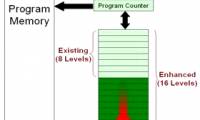
Techniques to exploit buffer overflows: Organize memory, stack, call functions, shellcode
this article covers buffer overflow that occurs on the stack and the technique of exploiting this common security error. this article consists of two parts: part 1: organizing memory, stack, function calls, shellcode and part 2: exploiting buffer overflow techniques
-

Error due to buffer overflow and how to fix it
basically, buffer overflow is caused by the user sending too much data to a program and part of this data is forced to store out of memory that the programmer has allocated.
-

Stack Overflow hits the hacker face, no significant damage is recorded
in a brief report released earlier today, stack overflow has reportedly recorded an attack that led hackers to successfully access their production systems.
-

What is Overflow? How to Detect and Prevent Data Overflow Errors in the System
overflow is also known as overflow error, this is a common term in the information technology industry.
-

Concept of Buffer in Node.js
net javascript is unicode encoded conveniently but not really good with binary data. when working with tcp streams or file systems, it is necessary to handle octal data streams. node.js provides buffer classes that allow raw data to be stored as an array of integers corresponding to external raw
-

The Linux machine can be remotely hacked with a poisoned DNS response
an important vulnerability was discovered on systemd, the init system and managed on a linux machine, allowing the hacker to cause a buffer overflow to execute malicious code on the target machine via dns feedback.
-

Overflow in CSS
the css overflow feature determines how content will display when it is too large for a given frame.
-

NVIDIA Jetson chipset contains a series of security holes that allow data theft, DDoS attacks
a series of new critical security vulnerabilities have been found in the jetson chip framework (nvidia) that could affect millions of active graphics cards worldwide.
-

How to fix table errors in Word overflow
error word overflow table can be corrected in 2 different ways and very simple to perform, helping to bring the table in word aligned correctly.
-

How to fix text overflow in Google Sheets
when we enter content in google sheets spreadsheet, the default text will overflow when importing multiple contents. if we resize each cell so that the text fits neatly in one cell, it will be very time consuming.
-

What is 51% attack? How does 51% attack work?
the 51% attack refers to a potential attack on the integrity of the blockchain system, in which a single malicious actor or organization tries to control more than half of the network's total hash power, .
-

What is a Replay Attack?
a replay attack occurs when a cybercriminal eavesdroves a communication over a secure network, intercepts it, then delays or resends the content, to get the recipient to do what the hacker wants.
-

How to clear the DNS cache buffer in Google Chrome
clearing the dns cache can help you troubleshoot host connectivity when accessing some websites. in this article, tipsmake.com will guide you to do that.
-

What is Volumetric DDoS Attack?
volumetric ddos attack is designed to overwhelm internal network capacity with large volumes of malicious traffic. volumetric ddos attack is usually performed against a specific target
-

Computer says waiting for buffer memory, how to fix it?
it's not uncommon for a computer to say it's waiting for a cache. however, many users still do not know how to handle it.
-

What is SS7 attack? What can hackers use it for?
an ss7 attack is a very dangerous attack method. an ss7 attack can be used to bypass two-factor authentication. so what specifically is the ss7 attack? what can a hacker do with an ss7 attack?
-

Types of data hiding in Excel - Part 2: How to hide cells, overflow text
continuing the 'extremely useful guide to all types of data hiding in excel'. tipsmake would like to introduce to you part 2: how to hide cells, overflow text ...
-

Analysis of an attack (Part 3)
in part 2 of this series, we have left all the necessary information required for an attack on the victim network. with that note, let's continue with a real attack. this attack follows the transmission of ecommerce