MessageLabs security company has transformed some virtual threats into painting works using malicious code created them.
Alex Dragulescu created images of six virtual threats from using the code detected by MessageLabs, including viruses, phishing scams, spam (spam), spyware (spyware) and Trojan malware. .
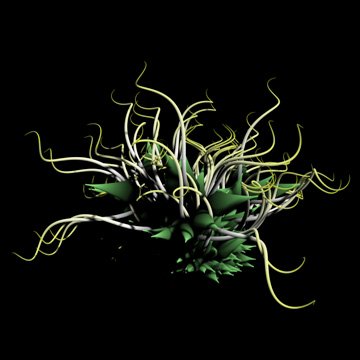
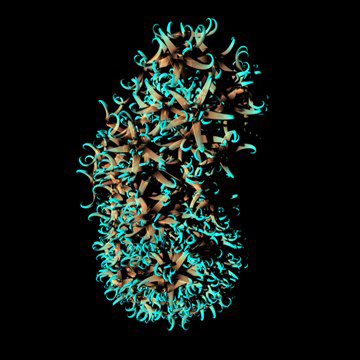
This is Ghost spy software that saves keyboard typing, screen capturing and visited Web sites.The information obtained can then be used for criminal purposes.
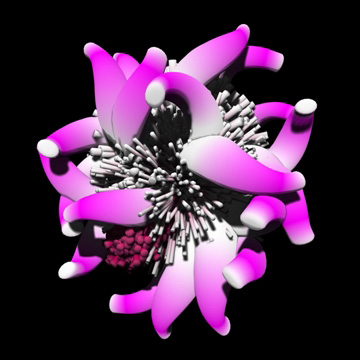
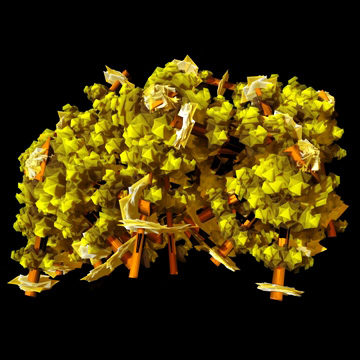
This beautiful version is Netsky - a worm that certainly threatens through email traffic.
This is Phishing1, the scam that requires victims to confirm personal information
such as address or bank account details to upgrade security for users.
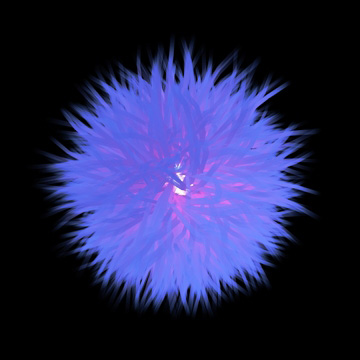
This is the code for spam Russian3, which uses images
to aim for personal self-doubt points like weight
or hair loss to convince them to register suspicious products or plans.
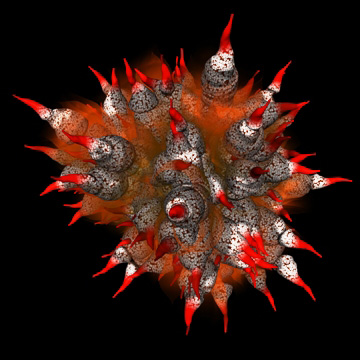
This is the Storm virus that has created an unprecedentedly large botnet of about
2 million Bonet poisoned computers are a group of computers that have been hacked
'occupy' and remote control to launch attacks on the network.
Trojanagentil3 is a decrypted Trojan code, constantly type
change to avoid security software.