Article on the subject of "gutmann method"
-

Learn about Gutmann data deletion method
the gutmann method is one of several software-based data sanitization methods, used in some file shredder and data destruction programs, to overwrite existing information on a hard drive or other storage device.
-

Learn about Gutmann data deletion method
the gutmann method is one of several software-based data sanitization methods, used in some file shredder and data destruction programs, to overwrite existing information on a hard drive or other storage device.
-

Method in HTTP
the set of common methods for http / 1.1 is defined below and this set of settings can be expanded based on the requirements. these method names are case-sensitive and they must be used in uppercase.
-

Anonymous method in C #
we have discussed that delegate is used to reference any method that has the same sign as in delegate. in other words, you can call a method that can be referenced by a delegate using that delegate object.
-

What is the Schneier (Data Sanitization) method?
the schneier method is a software-based data sanitization method used in some file shredder and data shredder programs to overwrite existing information on hard drives or other storage devices.
-

What is the Random Data method?
the random data method is a software-based data sanitization method, used in some file shredder and data shredder programs to overwrite existing information on hard drives or other storage devices.
-

Pomodoro 'tomato' method: Working focused, highly effective without fatigue
how can you work continuously for 4 - 5 hours (or more) and still be effective, do not feel tired and do not exhaust the idea? pomodoro - also known as tomato fruit is the method to increase the performance you need.
-

How trojan pretends to be a PDF file using the RLO . method
you cannot guarantee that a file is really an image, video, pdf or text file just by looking at the file extension. on windows, an attacker can execute a pdf file as if it were an exe file.
-

Limit records in MongoDB
to limit the records in mongodb, you need to use the limit () method. the limit () method takes a parameter in a numeric format, which is the document number you want to display.
-

Learn about the Write Zero method
many file shredder and data destruction programs support data sanitization method based on write zero software to overwrite existing data on storage devices such as hard drives.
-

Update Document in MongoDB
the update () method updates the values in the existing document while the save () method replaces the existing document with the transmitted document in that save () method.
-

How to remove payment method from Google Play
maybe your google play payment card has expired, or you want to switch to a new bank. here's how to remove a payment method from your google play account.
-

Effective excel learning method
excel, one of the most important and indispensable computer skills, and tipsmake share the most effective 'excel learning method'
-

Scientists have created the world's first unbreakable encryption chip, including quantum computers
after years of research, a group of scientists recently announced the successful development of the world's first 'completely unbreakable' encryption method.
-

Response object in Node.js
the object res represents the http response that the express application sends when receiving an http request.
-

Learn about the method of clearing DoD 5220.22-M data
dod 5220.22-m is a software-based data sanitization method, used in various file shredder and data shredder programs to overwrite existing information on hard drives or other storage devices.
-

Learn about the NAVSO P-5239-26 method
navso p-5239-26 is a software-based data sanitization method used in various file shredder and data shredder programs to overwrite existing information on a hard drive or other storage device.
-

What is Data Sanitization? Are there any Data Sanitization methods?
the data sanitization method is a specific way in which a data destruction program or file destruction software overwrites data on a hard drive or other storage device.
-

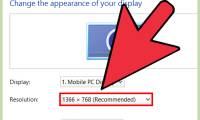
How to Zoom Out on a PC
there are several ways to zoom out on your computer. this wikihow will help you zoom out on a pc. select the page you want to zoom out of by clicking on it. this method is best for most users. it's the quickest and easiest, especially for...
-

What is the HMG IS5 method?
hmg is5 (infosec standard 5) is a software-based data sanitization method, used in some file shredder and data shredder programs to overwrite existing information on a hard drive or other storage device.
-

Request object in Node.js
the req object represents the http request and has properties for the request query string, parameters, body, http header ...